18-Year-Old Hacker Gets 3 Years in Prison for Massive Twitter ‘Bitcoin Scam’ Hack

A Florida teen accused of masterminding the hacks of several high-profile Twitter accounts last summer as part of a widespread cryptocurrency scam pled guilty to fraud charges in exchange for a three-year prison sentence.
Graham Ivan Clark, 18, will also serve an additional three years on probation.
The development comes after the U.S. Department of Justice (DoJ) charged Mason Sheppard (aka Chaewon), Nima Fazeli (aka Rolex), and Clark (then a juvenile) with conspiracy to commit wire fraud and money laundering.
Specifically, 30 felony charges were filed against Clark, including one count of organized fraud, 17 counts of communications fraud, one count of fraudulent use of personal information with over $100,000 or 30 or more victims, 10 counts of fraudulent use of personal information, and one count of access to computer or electronic device without authority.
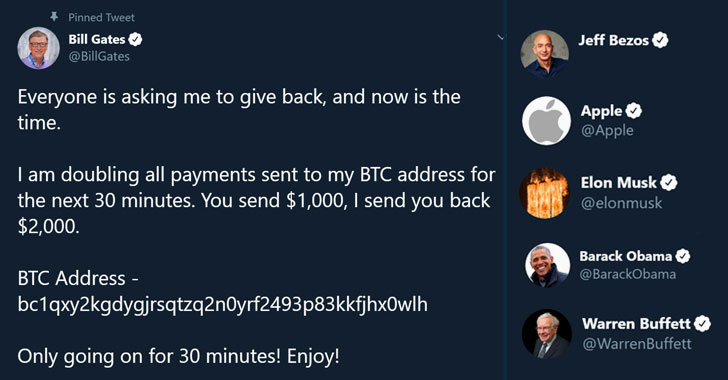
On July 15, 2020, Twitter suffered one of the biggest security lapses in its history after the attackers managed to hijack nearly 130 high-profile Twitter accounts pertaining to politicians, celebrities, and musicians, including that of Barack Obama, Kanye West, Joe Biden, Bill Gates, Elon Musk, Jeff Bezos, Warren Buffett, Uber, and Apple.
The broadly targeted hack posted similarly worded messages urging millions of followers of each profile to send money to a specific bitcoin wallet address in return for larger payback. The scheme netted about $117,000 in bitcoin before it was shut down.
Subsequent investigation into the incident revealed that Clark and the other attackers seized the accounts after stealing Twitter employees’ credentials through a successful phone spear-phishing attack, subsequently using them to gain access to the company’s internal network and account support tools, change user account settings, and take over control.
“By obtaining employee credentials, they were able to target specific employees who had access to our account support tools. They then targeted 130 Twitter accounts – Tweeting from 45, accessing the DM inbox of 36, and downloading the Twitter Data of 7,” the company said on July 31.
Additionally, the three individuals attempted to monetize this entrenched access by selling the hijacked…


