Active Threat Alerts
Iranian Islamic Revolutionary Guard Corps-Affiliated Cyber Actors Exploiting Vulnerabilities for Data Extortion and Disk Encryption for Ransom Operations
Summary
Actions to take…
September 14, 2022/by SecureTechActions to take…
#StopRansomware: Vice Society | CISA
Summary
Actions to take…
September 6, 2022/by SecureTechActions to take…
Threat Actors Exploiting Multiple CVEs Against Zimbra Collaboration Suite
Actions for ZCS administrators to take today to mitigate malicious…
August 17, 2022/by SecureTech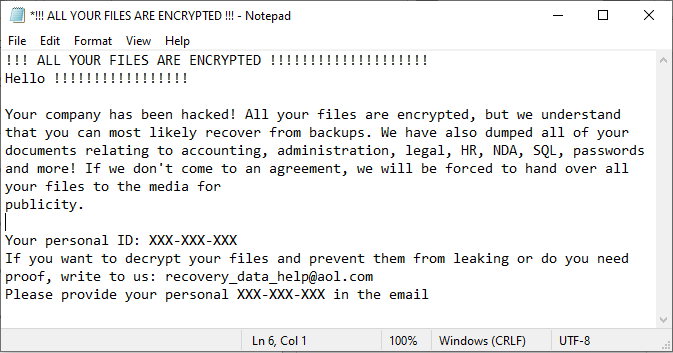
AA22-223A: #StopRansomware: Zeppelin Ransomware
Original release date: August 11, 2022SummaryActions to take…
August 12, 2022/by SecureTech2021 Top Malware Strains | CISA
Agent Tesla
alert any any -> any any (msg:”HTTP…
August 4, 2022/by SecureTechalert any any -> any any (msg:”HTTP…
North Korean State-Sponsored Cyber Actors Use Maui Ransomware to Target the Healthcare and Public Health Sector
Summary
The Federal Bureau…
July 7, 2022/by SecureTechThe Federal Bureau…
#StopRansomware: MedusaLocker | CISA
Summary
Actions to take…
June 30, 2022/by SecureTechActions to take…
Malicious Cyber Actors Continue to Exploit Log4Shell in VMware Horizon Systems
Actions to take today:• Install fixed builds, updating all…
June 23, 2022/by SecureTechPeople’s Republic of China State-Sponsored Cyber Actors Exploit Network Providers and Devices
Best Practices• Apply patches as soon as possible• Disable…
June 8, 2022/by SecureTechKarakurt Data Extortion Group | CISA
Actions to take today to mitigate cyber threats from ransomware:•…
June 2, 2022/by SecureTechThreat Actors Exploiting F5 BIG-IP CVE-2022-1388
Actions for administrators to take today:• Do not expose…
May 19, 2022/by SecureTechThreat Actors Chaining Unpatched VMware Vulnerabilities for Full System Control
The Cybersecurity and Infrastructure Security Agency (CISA)…
May 18, 2022/by SecureTechWeak Security Controls and Practices Routinely Exploited for Initial Access
Best Practices to Protect Your Systems:• Control access.•…
May 17, 2022/by SecureTechProtecting Against Cyber Threats to Managed Service Providers and their Customers
Tactical actions for MSPs and their customers to take today:•…
May 11, 2022/by SecureTech2021 Top Routinely Exploited Vulnerabilities
This joint Cybersecurity Advisory (CSA) was coauthored by cybersecurity…
April 28, 2022/by SecureTechRussian State-Sponsored and Criminal Cyber Threats to Critical Infrastructure
Russian State-Sponsored Cyber Operations
Russian state-sponsored…
April 21, 2022/by SecureTechRussian state-sponsored…

TraderTraitor: North Korean State-Sponsored APT Targets Blockchain Companies
Actions to take today to mitigate cyber threats to cryptocurrency:•…
April 19, 2022/by SecureTechAPT Cyber Tools Targeting ICS/SCADA Devices
Summary
Actions to Take…
April 13, 2022/by SecureTechActions to Take…
Tactics, Techniques, and Procedures of Indicted State-Sponsored Russian Cyber Actors Targeting the Energy Sector
Tactic
Technique
Use
Detection/Mitigations
Reconnaissance…
March 25, 2022/by SecureTechTechnique
Use
Detection/Mitigations
Reconnaissance…
Strengthening Cybersecurity of SATCOM Network Providers and Customers
Actions to Take Today:• Use secure methods for authentication.•…
March 18, 2022/by SecureTechRussian State-Sponsored Cyber Actors Gain Network Access by Exploiting Default Multifactor Authentication Protocols and “PrintNightmare” Vulnerability
Summary
Multifactor Authentication…
March 16, 2022/by SecureTechMultifactor Authentication…
Destructive Malware Targeting Organizations in Ukraine
Actions to Take Today:• Set antivirus and antimalware programs…
February 26, 2022/by SecureTech
Iranian Government-Sponsored Actors Conduct Cyber Operations Against Global Government and Commercial Networks
Summary
Actions to Take…
February 24, 2022/by SecureTechActions to Take…
New Sandworm Malware Cyclops Blink Replaces VPNFilter
Summary
The Sandworm actor,…
February 23, 2022/by SecureTechThe Sandworm actor,…
Russian State-Sponsored Cyber Actors Target Cleared Defense Contractor Networks to Obtain Sensitive U.S. Defense Information and Technology
Summary
Actions to Help…
February 17, 2022/by SecureTechActions to Help…
2021 Trends Show Increased Globalized Threat of Ransomware
Summary
Immediate Actions…
February 10, 2022/by SecureTechImmediate Actions…