Amit Serper joins Sternum as Director of Security Research
Sternum welcomes Amit Serper, an international cybersecurity expert, as its new Director of Security Research. As a veteran cybersecurity professional with a record of excellence in the field, Amit bolsters Sternum’s vast research capabilities with his decades of expertise in reverse engineering, vulnerability exploitation, and ethical hacking.
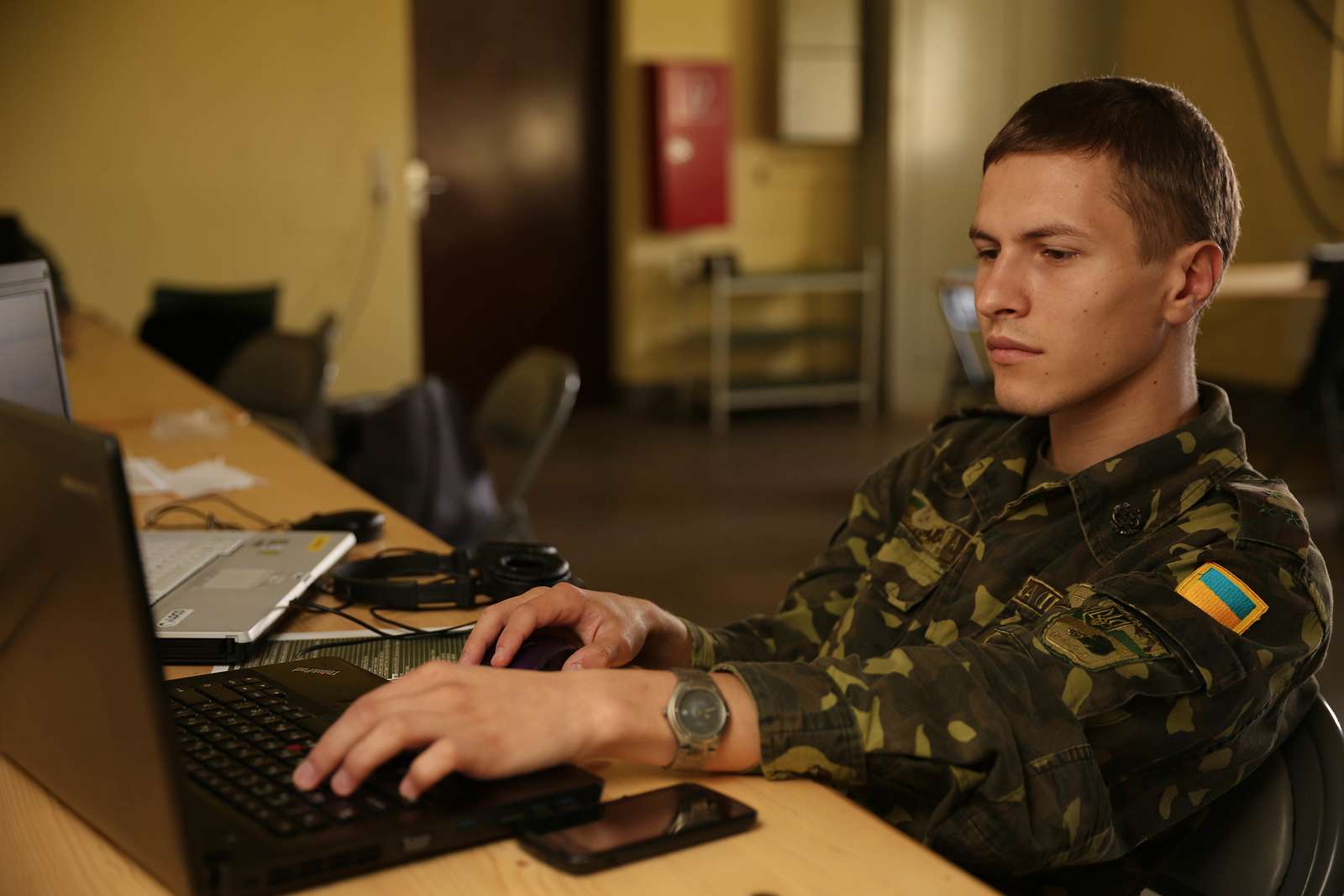
The global total of cyberattacks is surging year on year as hackers exploit the ever-growing trend toward digitalization. An uptick in international tensions is further exacerbating the trend as Russia allegedly unleashed its cyber-arsenal on Ukraine in the run-up to its ground incursion. Previously, the U.S. intelligence community blamed Moscow for NotPetya malware attacks on Ukrainian networks, which destroyed sensitive data on a variety of servers and spilled out beyond Ukraine to wreak havoc on businesses.
Amit Serper, who found a “vaccine” for NotPetya, now joins Sternum’s leadership team to lend the company his vast expertise in cybersecurity. Amit will be in charge of Sternum’s security research, leading its team of cybersecurity experts as they work to transform the IoT defense paradigm.
Before joining Sternum, Amit worked as the Director of Security Research for Akamai Technologies, a U.S. cloud and cybersecurity giant, where he focused on enterprise network protection. Prior to that, he held the offices of North American VP of Security Research for Guardicore, a network segmentation company, ahead of its acquisition by Akamai. Amit also held a number of positions in Cybereason, working his way up from Senior Security Researcher to VP for Security Strategy. His private sector career followed years of service in the Israeli military and intelligence, where he took on a variety of security roles and projects.
Sternum’s single-click security solution gives any connected device the ability to protect itself against hacking attempts in real-time. It seeks out the generic fingerprints of various attack types such as command injection and buffer overflow to strike the attempted attack down and protect the runtime integrity of the secured device against both zero-day and one-day attacks. Its design fosters a proactive…