Are embedded devices the next ransomware target? – TechCrunch
2021 will be remembered as the year that ransomware gangs turned their attention to critical infrastructure, targeting companies built around manufacturing, energy distribution, and food production.
The Colonial Pipeline ransomware alone resulted in the shutdown of 5,500 miles of pipeline over fears that the ransomware attack on its IT network would spread to the operational network that controls the pipeline for distributing fuel.
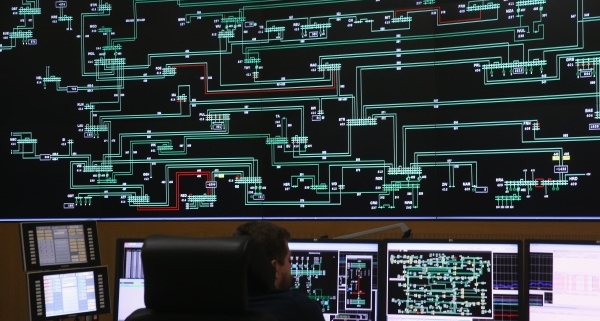
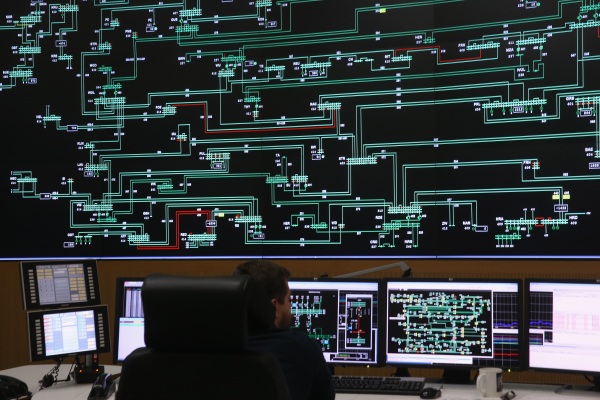
Operational technology (OT) networks control the devices critical to the continued operations of production lines, power plants, and energy supplies, and as such are typically segmented from a company’s internet-facing IT networks to better isolate critical hardware from cyberattacks. Successful attacks against OT networks are rare, but in the wake of the Colonial ransomware attack, CISA warned of a growing threat for critical infrastructure owners.
Now security researchers are warning of the risks posed by the embedded devices that sit on those OT networks. Red Balloon Security, a security provider for embedded devices, found in new research that it’s possible to deploy ransomware on embedded systems that are used in real-world networks.
The company said it found vulnerabilities in the Schneider Electric Easergy P5 protection relay, a device that’s key to the operation and stability of the modern electric grids by triggering circuit breakers if a fault is discovered.
This vulnerability could be exploited to deploy a ransomware payload, a “sophisticated but reproducible” process that Red Balloon said it achieved. A Schneider Electric spokesperson told TechCrunch “it is extremely vigilant of cyber threats,” and that “upon learning of the vulnerabilities with the Schneider Electric Easergy P5 protection relay, we worked immediately to resolve them.”
Ang Cui, founder and co-CEO of Red Balloon told TechCrunch that while ransomware attacks have hit IT networks of critical infrastructure providers, a successful compromise of an OT embedded device can be “far more damaging.”
“Companies are not used to or experienced in recovering from an attack on the embedded devices themselves,” he said. “If the device is…