Beware of Exposed Linux Ports
Coinmining accounted for more cases of malware than any other family.
More than 13 million Linux-based cloud environments face a malware event, according to Trend Micro.
The company recently unveiled its 2021 1H Linux Threat Report, which shows threat actors are paying close attention to Linux users.
Although popular society typically talks about Microsoft Windows and macOS when it comes to operating systems, Trend Micro notes that all of the largest supercomputers in the world use Linux. Moreover, a W3Techs survey found that more than half (51%) of the world’s largest 1,000 websites use Linux. Linux users also highly populate the Trend Micro workload security customer base.
“It’s safe to say that Linux is here to stay, and as organizations continue to move to Linux-based cloud workloads, malicious actors will follow,” said Aaron Ansari, Trend Micro’s vice president of cloud security.
Threat Numbers
And the numbers show that the malicious actors have arrived. Trend Micro in one search found 14 million results for exposed, internet-connected devices that use Linux operating systems.
Approximately 19 million machines ran servers with the exposed “port 22.” The majority of those machines reside in the U.S. Trend Micro urged companies to close up those ports.
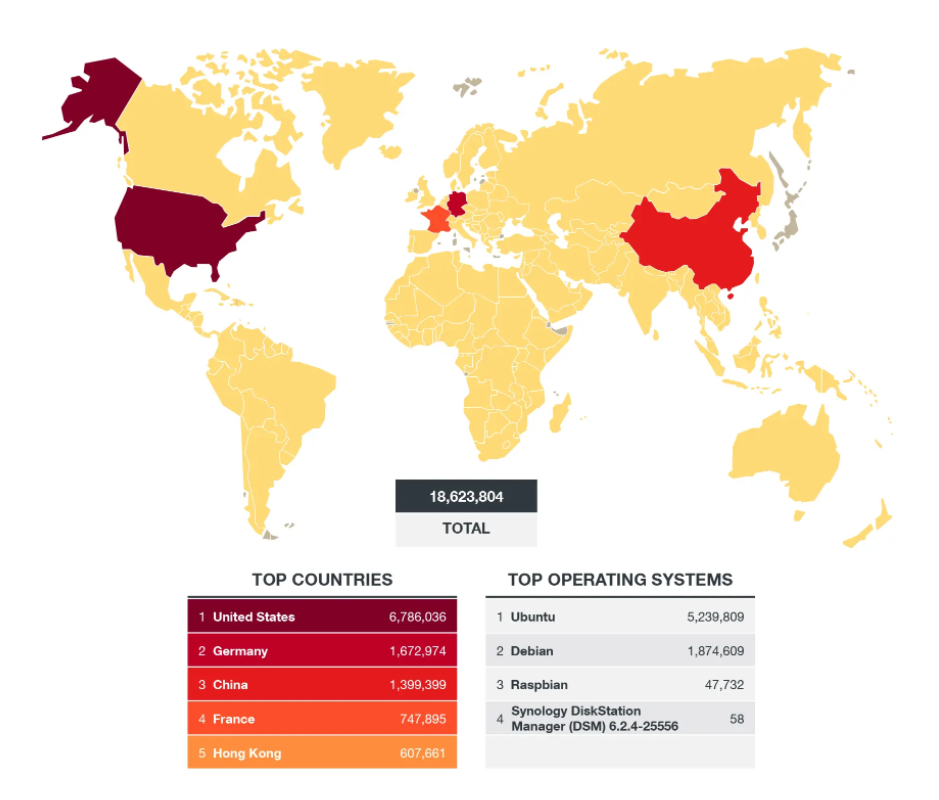
Source: Trend Micro 1H 2021 Linux Threat Report
Most of the detected threats occurred in end-of-life systems. In particular, CentOS version 7.4 through 7.9 accounted for 44% of detections.
Trend Micro also broke down the most prevalent malware families affecting Linux servers in the first half of 2021. Coinminers took the top prize, capitalizing on cryptocurrency mining trends. Web shells, which include the recent Microsoft Exchange Attack, came in second. Ransomware and trojans trailed in third and fourth, respectively.
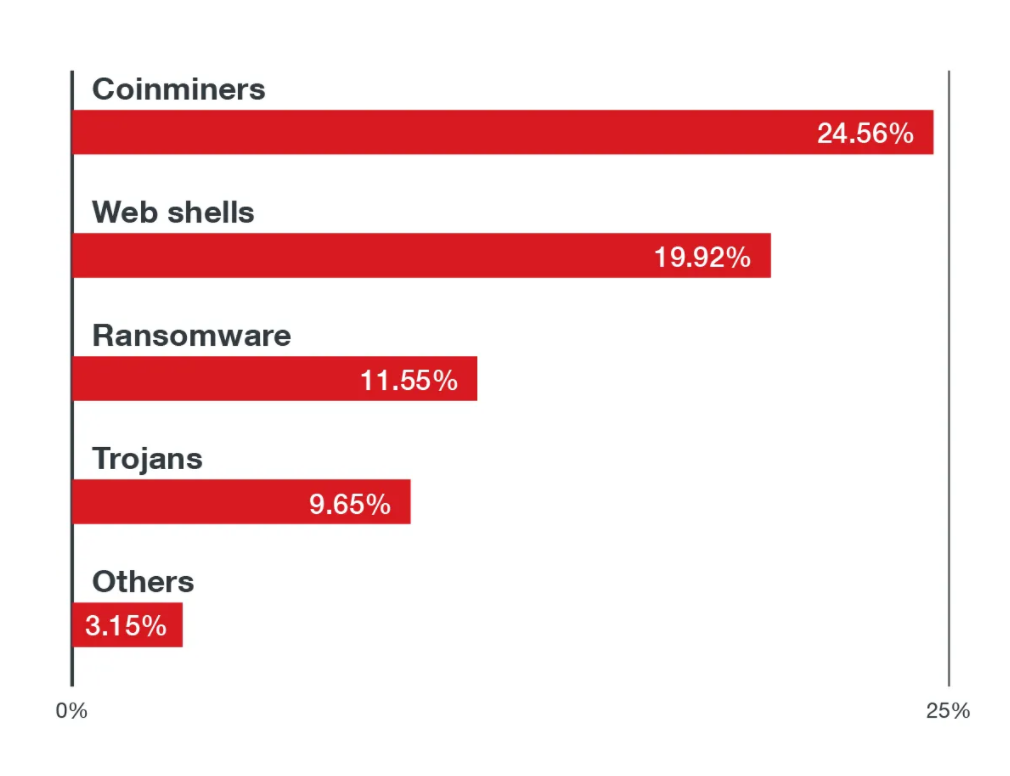
Source: Trend Micro 1H 2021 Linux Threat Report
Trend Micro in July released the results of its ransomware study.


