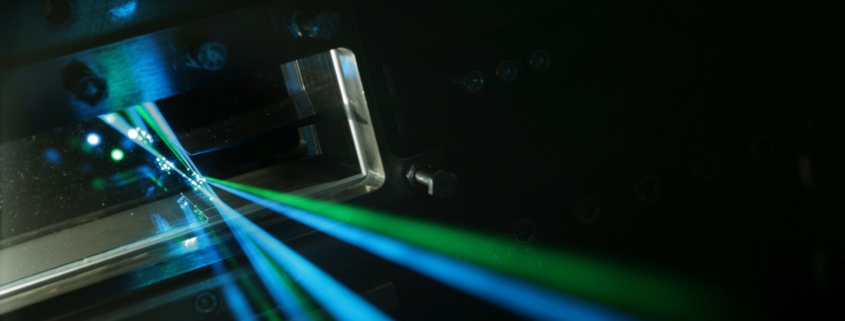
Computer attacks with laser light
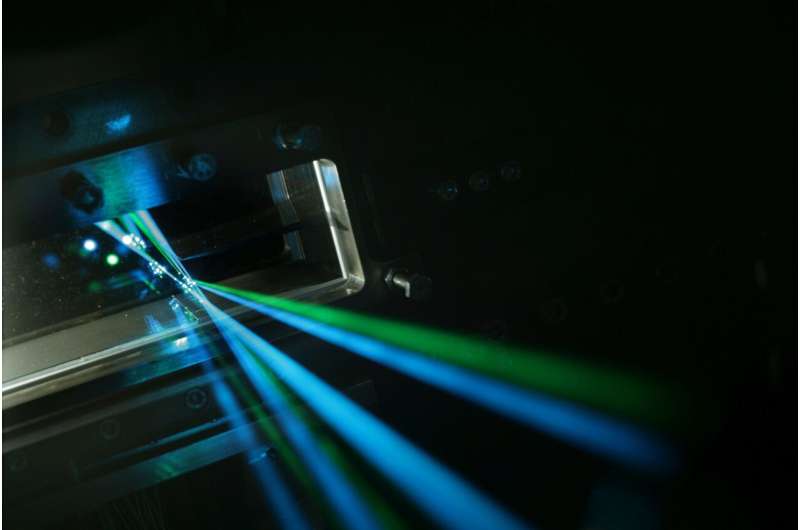
Computer systems that are physically isolated from the outside world (air-gapped) can still be attacked. This is demonstrated by IT security experts of the Karlsruhe Institute of Technology (KIT) in the LaserShark project. They show that data can be transmitted to light-emitting diodes of regular office devices using a directed laser. With this, attackers can secretly communicate with air-gapped computer systems over distances of several meters. In addition to conventional information and communication technology security, critical IT systems need to be protected optically as well.
Hackers attack computers with lasers. This sounds like a scene from the latest James Bond movie, but it actually is possible in reality. Early December 2021, researchers of KIT, TU Braunschweig, and TU Berlin presented the LaserShark attack at the 37th Annual Computer Security Applications Conference (ACSAC). This research project focuses on hidden communication via optical channels. Computers or networks in critical infrastructures are often physically isolated to prevent external access. “Air-gapping” means that these systems have neither wired nor wireless connections to the outside world. Previous attempts to bypass such protection via electromagnetic, acoustic, or optical channels merely work at short distances or low data rates. Moreover, they frequently allow for data exfiltration only, that is, receiving data.
Hidden optical channel uses LEDs in commercially available office devices
The Intelligent System Security Group of KASTEL—Institute of Information Security and Dependability of KIT, in cooperation with researchers from TU Braunschweig and TU Berlin, have now demonstrated a new attack: With a directed laser beam, an adversary can introduce data into air-gapped systems and retrieve data without additional hardware on-side at the attacked device. “This hidden optical communication uses…