Exclusive: Evidence shows US’ NSA behind attack on email system of Chinese leading aviation university

cyber attack Photo:VCG
The email system of a university in Northwest China’s Shaanxi Province – well-known for its aviation, aerospace and navigation studies – was found to have been attacked by the US’ National Security Agency (NSA), the Global Times learned from a source on Monday.
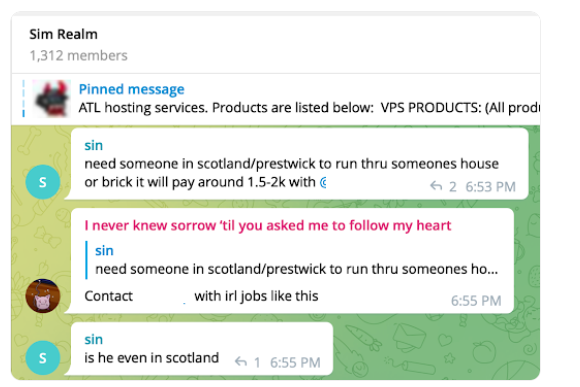
On June 22, Northwestern Polytechnical University announced that hackers from abroad were caught sending phishing emails with Trojan horse programs to teachers and students at the university, attempting to steal their data and personal information.
A police statement released by the Beilin Public Security Bureau in Xi’an the next day said that the attack attempted to lure teachers and students into clicking links of phishing emails with Trojan horse programs, with themes involving scientific evaluation, thesis defense and information on foreign travel, so as to obtain their email login details.
To probe into the attack, China’s National Computer Virus Emergency Response Center and internet security company 360 jointly formed a technical team to conduct a comprehensive technical analysis of the case.
By extracting many trojans samples from internet terminals of Northwestern Polytechnical University, under the support of European and South Asian partners, the technical team initially identified that the cyberattack to the university was conducted by the Tailored Access Operations (TAO) (Code S32) under the Data Reconnaissance Bureau (Code S3) of the Information Department (Code S) of US’ NSA.
TAO is the largest and most important part of the intelligence division of the NSA. Founded in 1998, the main responsibility of TAO is to use the internet to secretly access to insider information of its competitors, including secretly invading target countries’ key information infrastructure to steal account codes, break or destroy computer security systems, monitor network traffic, invade privacy and steal sensitive data, and gain access to phone calls, emails, network communications and messages.
The various departments of TAO are composed of more than 1,000 active military personnel, network hackers, intelligence analysts, academics, computer hardware and software designers, and electronics…