Google fixes sixth Chrome zero-day exploited in the wild this year

Google has released Chrome 91.0.4472.101 for Windows, Mac, and Linux to fix 14 security vulnerabilities, with one zero-day vulnerability exploited in the wild and tracked as CVE-2021-30551.
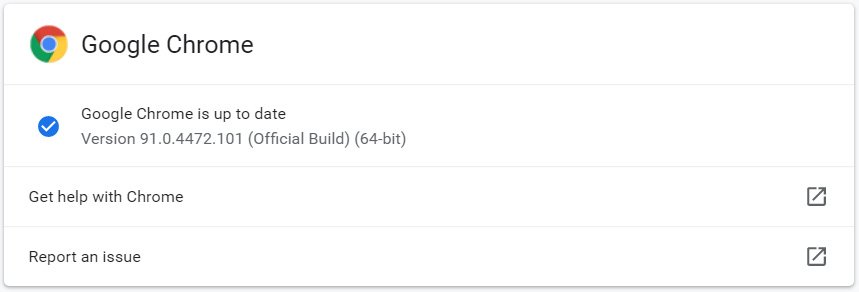
Google Chrome 91.0.4472.101 has started rolling out worldwide and will become available to all users over the next few days.
Google Chrome will automatically attempt to upgrade the browser the next time you launch the program, but you can perform a manual update by going to Settings > Help > ‘About Google Chrome
Six Chrome zero-days exploited in the wild in 2021
Few details regarding today’s fixed zero-day vulnerability are currently available other than that it is a type confusion bug in V8, Google’s open-source and C++ WebAssembly and JavaScript engine.
The vulnerability was discovered by Sergei Glazunov of Google Project Zero and is being tracked as CVE-2021-30551.
Google states that they are “aware that an exploit for CVE-2021-30551 exists in the wild.”
Shane Huntley, Director of Google’s Threat Analysis Group, says that this zero-day was utilized by the same threat actors using the Windows CVE-2021-33742 zero-day fixed yesterday by Microsoft.
Chrome in-the-wild vulnerability CVE-2021-30551 patched today was also from the same actor and targeting.
Thanks to Chrome team for also patching within 7 days.https://t.co/1RDbbuiBfY https://t.co/Ap9dEq98Cy— Shane Huntley (@ShaneHuntley) June 9, 2021
Today’s update fixes Google Chrome’s sixth zero-day exploited in attacks this year, with the other five listed below:
- CVE-2021-21148 – February 4th, 2021
- CVE-2021-21166 – March 2nd, 2021
- CVE-2021-21193 – March 12th, 2021
- CVE-2021-21220 – April 13th, 2021
- CVE-2021-21224 – April 20th, 2021
In addition to these vulnerabilities, news broke yesterday of a threat actor group known as Puzzlemaker that is chaining together Google Chrome zero-day bugs to escape the browser’s sandbox and install malware in Windows.
“Once the attackers have used both the Chrome and Windows exploits to gain a foothold in the targeted system, the stager module downloads and executes a more complex malware dropper from a remote server,” the researchers said.
Microsoft…


