Hacker posts exploits for over 49,000 vulnerable Fortinet VPNs

A hacker has posted a list of one-line exploits to steal VPN credentials from almost 50,000 Fortinet VPN devices.
Present on the list of vulnerable targets are domains belonging to high street banks and government organizations from around the world.
Researchers find thousands of targets
The vulnerability being referred to here is CVE-2018-13379, a path traversal flaw impacting a large number of unpatched Fortinet FortiOS SSL VPN devices.
By exploiting this vulnerability, unauthenticated remote attackers can access system files via specially crafted HTTP requests.
The exploit posted by the hacker lets attackers access the sslvpn_websession files from Fortinet VPNs to steal login credentials. These stolen credentials could then be used to compromise a network and deploy ransomware.
Although the 2018 bug was publicly disclosed over a year ago, researchers have spotted around 50,000 targets that can still be targeted by attackers.
This week, threat intelligence analyst Bank_Security found a hacker forum thread where a threat actor shared a large 49,577 device list of such exploitable targets
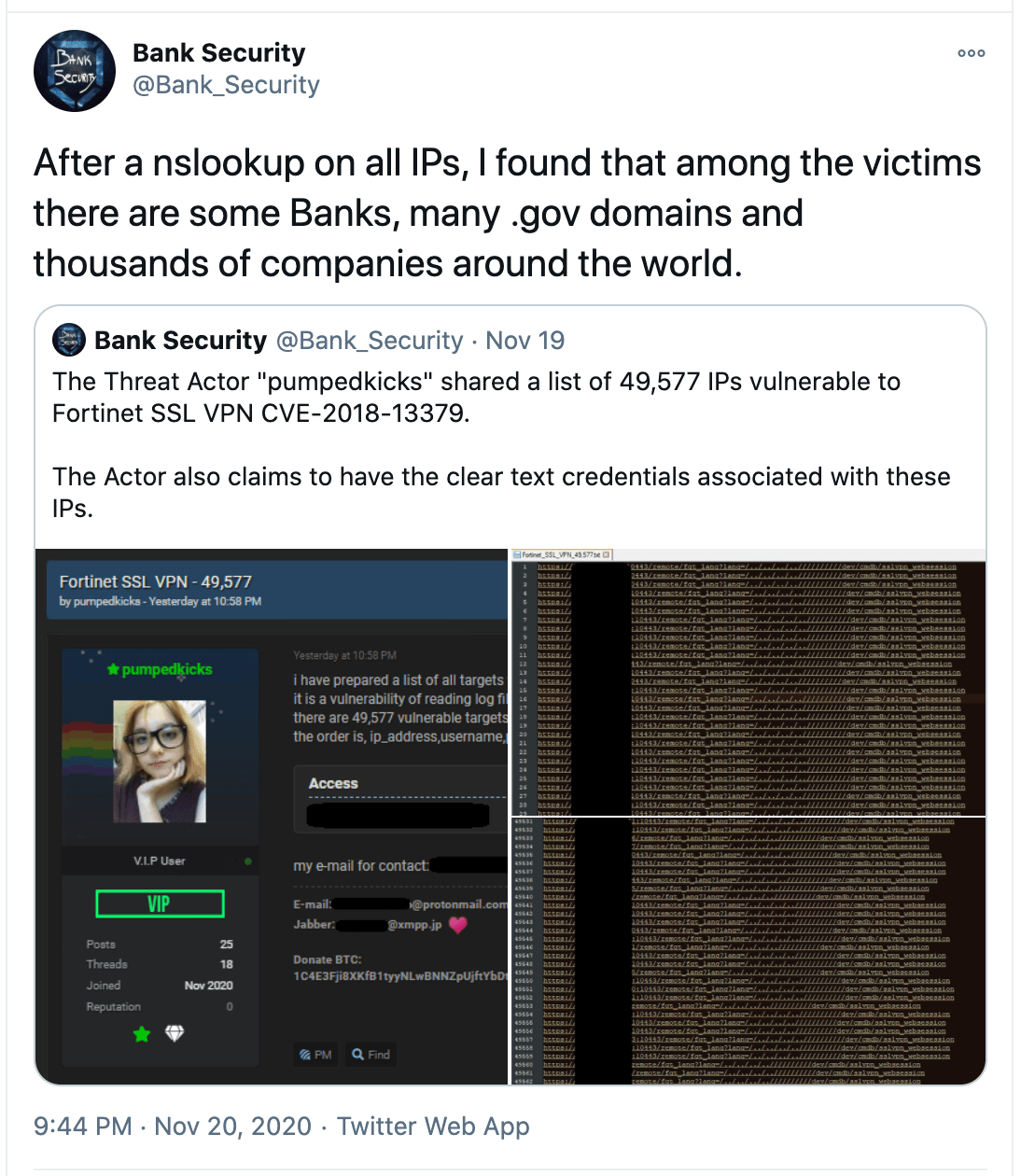
Source: Twitter
After analyzing the list, it was found that the vulnerable targets included government domains from around the world, and those belonging to well-known banks and finance companies.
Banks, finance, and govt organizations vulnerable
As observed by BleepingComputer, out of the 50,000 domains, over four dozen belonged to reputable banking, finance, and governmental organizations.
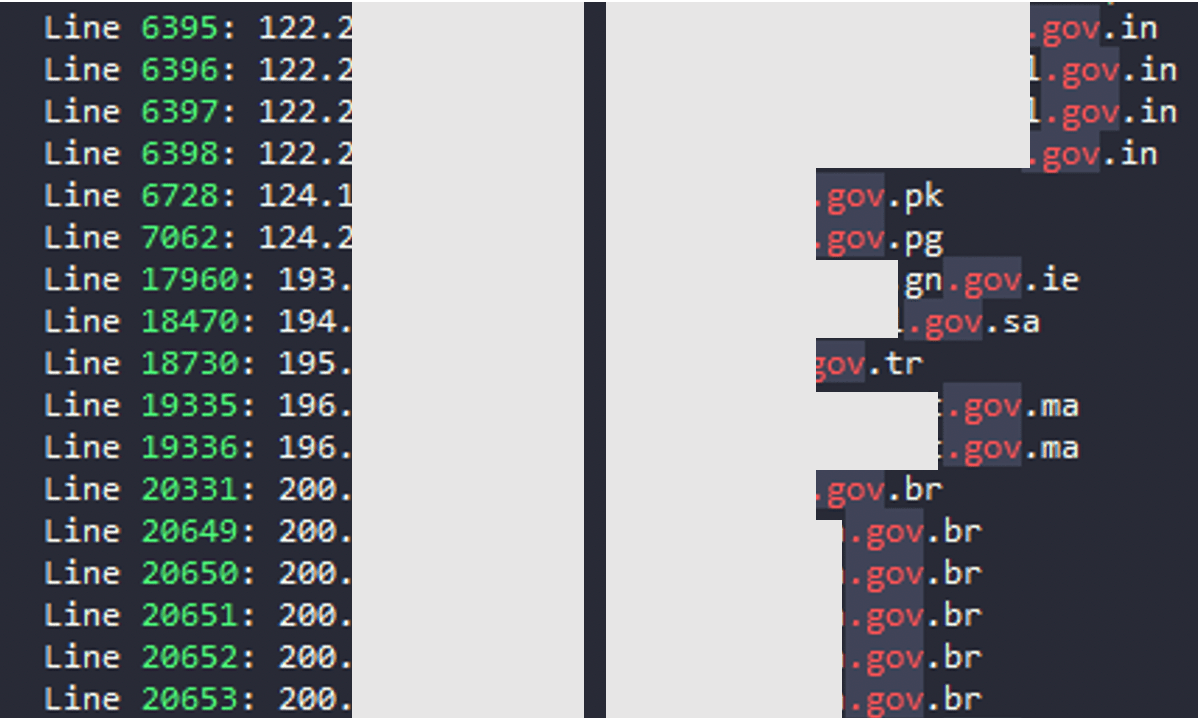
Source: BleepingComputer
Bank Security told BleepingComputer after he saw the forum post, he started analyzing the list of IPs to identify what all organizations were impacted.
“To better find out which companies were impacted, I launched an nslookup on all the IPs on the list and for many of them, I found the associated domain.”
The analyst then refined the obtained results to identify domain names associated with organizations of interest and notable banks.
The analyst further told BleepingComputer, although this is an old bug that is trivial…

