Hacker Shows How Gas Pumps Are Security Swiss Cheese And Easy Targets For Thieves
As gas prices continue to rise, some shadowy figures are looking for “alternative” method to acquire fuel, whether legal or not. One such method, specifically hacking a gas pump, has led to the recent theft of 400 gallons of fuel at a High Point gas station in North Carolina. However, this is not the only incidence of this happening, and as it turns out, gas pumps are surprisingly vulnerable to being hacked.
Earlier this week, a video surfaced of a man stealing gas for himself and other vehicles that arrived after the gas station had closed. Police and news outlets claim that the person pointed a device at the gas pump to release the dispenser to help fill up several cars waiting for free gas, leading to the theft of approximately $1600 in fuel. It is speculated that the thieves used a “special remote to alter the mechanics of the gas pump that puts it in ‘dispense mode,’ dispensing hundreds of gallons of gas for free,” according to Petroleum Technician Trey Barker, who spoke with Fox 8 in North Carolina. He continued, stating, “The reason dispensers have this option is so petroleum technicians, and NC Weight and Measures can test and calibrate dispensers.”

Interestingly, this theft is not the only one in recent years and is not the only option thieves have. In 2018, Kaspersky Labs found a basic web interface on a Linux-based controller unit in an embedded box at a gas station somewhere in the US. Following this discovery, it was found that this site is “responsible for managing every component of the station, including dispensers, payment terminals and more,” at the heart of the gas station. However, this was not the only gas station at risk, as there were at least 1,000 others with similar infrastructure exposed to the internet.
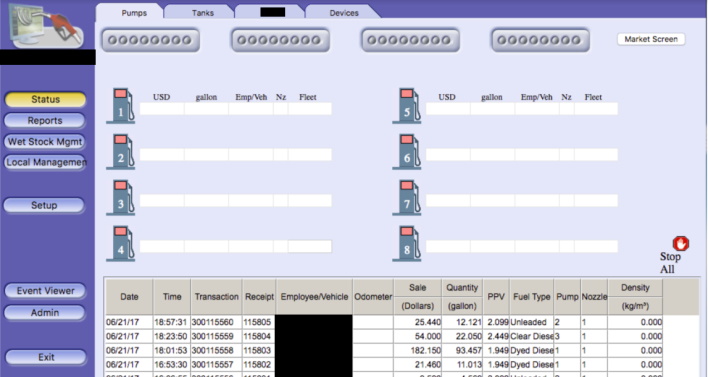
It is likely that other gas pump brands may use a similar configurations that could be exposed as well, and we might not know about them yet. In any event, default credentials for these web interfaces are sometimes not changed, allowing easy access into these systems. Besides this, there might also be…


