How to face the new challenges in an ever-expanding – and risky – internet environment
Two decades ago, we kept everything relatively simple by containing our organization’s technology footprint within the closed fortress that was the corporate network. The IT staff determined which tools to deploy, and the security team figured out how to best protect them and the network.
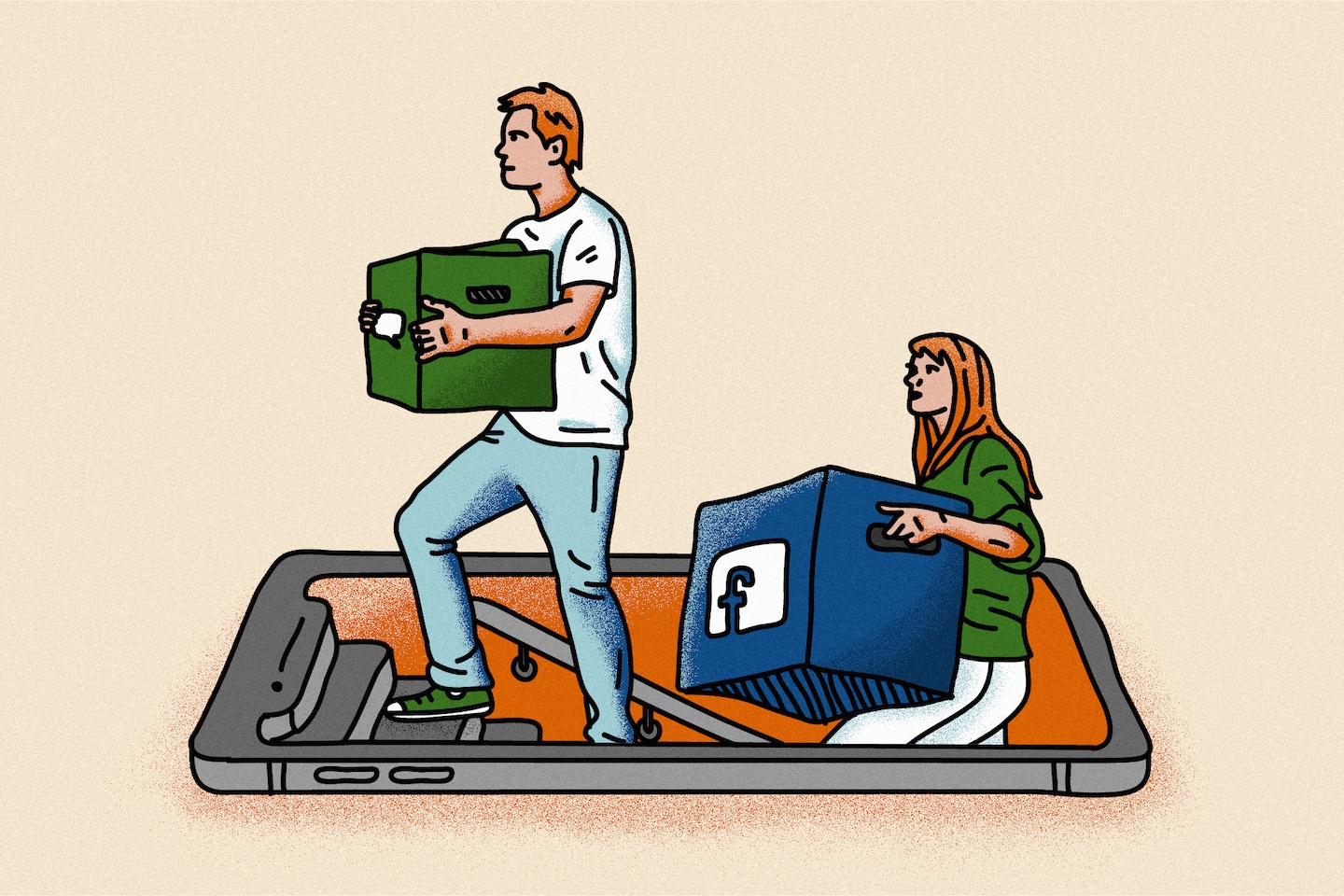
This seems a distant memory now, thanks to modern innovation: Work-from-home (WFH) arrangements continue to transform the traditional office culture, with spikes in cloud adoption, shadow IT, and Bring Your Own … Everything. The resulting widespread connectivity has boosted productivity. But it has also ushered in a new era of exposure because of a vastly increased attack surface.
Subsequently, chief information security officers (CISOs) and their teams can no longer afford to view their roles as an “after the fact,” reactive responsibility. They must instead take proactive steps to identify all internet-facing assets from the very beginning and protect them. With improved visibility and a “security first” commitment, companies can operate with peace of mind.
To illustrate this, we recently published research in which we evaluated the presence of a variety of risks and vulnerabilities in random samples of 2.2 million hosts in our Universal Internet Dataset (UIDS). Here’s what we found:
- WFH brings new challenges. Connecting remotely, employee-users are expanding the attack surface, although it’s an unintended result of their actions in most cases. Post-pandemic remote work has driven a 59% increase in the use of tools and devices not approved by IT (commonly called shadow IT), leading to unmanaged devices/services because IT and security teams are left out of the conversation. What’s more, we have found that organizations now use an average of 44 different domain registrars and 17 hosting providers – another likely outcome of shadow IT that further contributes to visibility issues.
- Misconfigurations and exposures create the most risks. Misconfigurations – such as unencrypted services, insufficient or missing security controls, and self-signed certificates – account for about 60% of internet risks. Exposures of services, devices and information represent 28%.
- Exposures are not…