Interpol arrests Moroccon hacker over global phishing, malware scam
“Dr. Hex” is accused of defacing websites, carrying out phishing attacks and malware campaigns.
An alleged malicious hacker and a cybercriminal who goes by the alias “Dr. Hex” has been arrested in Morocco after a two-year-long investigation.
Dubbed Op Lyrebird; authorities involved in the Operation included Moroccan police, International Criminal Police Organization – INTERPOL, and Russian cybersecurity company Group-IB.
In a statement this Tuesday, Interpol revealed that cyber attacks carried out by “Dr. Hex” involved, global phishing scams and carding activities such as credit card fraud against thousands of unsuspected victims.
According to authorities, the threat actor’s prime targets were French-speaking communications companies, multinational companies, and multiple banks that suffered malware attacks allegedly perpetrated by the accused.
“Dr. Hex” is also accused of targeting private, business, and government websites and defacing their homepage to a modified one displaying political and self-praising messages.
Deface page left by the hacker (Image: Hackread.com)
Although authorities believe “Dr. Hex” defaced 134 domains and sub-domains between 2009 and 2018, Hackread.com managed to save a screenshot showing the hacker’s last defacement was in 2019.
The following screenshot shows a list of websites that were defaced by the hacker. These sites belonged to different countries and sectors around the world.
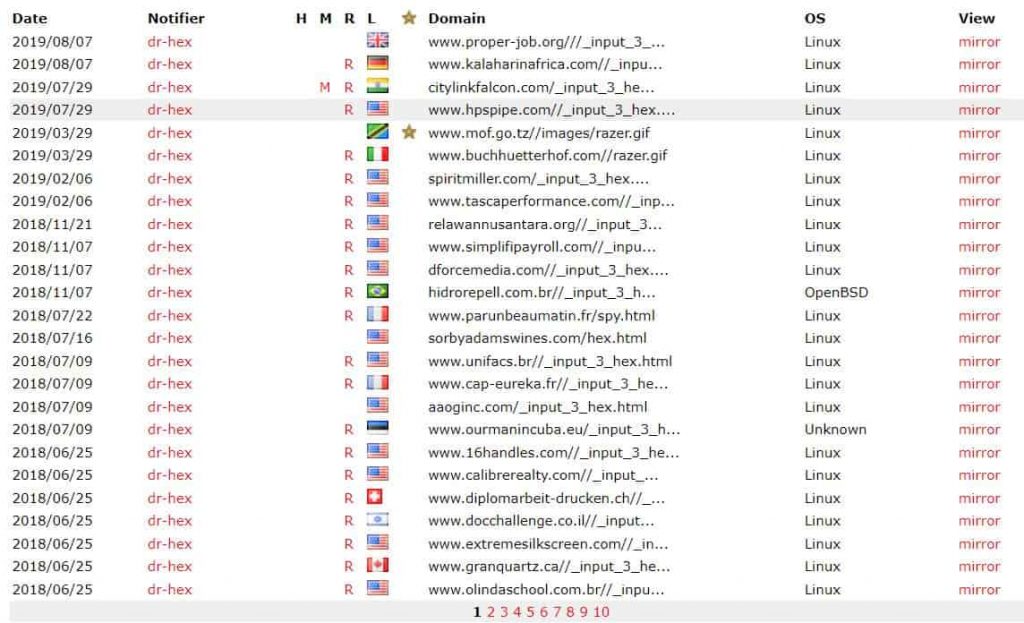
Image: Hackread.com
As for his phishing scams; the hacker used modified pages modified with data-stealing scripts. Once the victim clicked on the link it opened an authentic-looking login page for banks and other targeted companies. Once login credentials were entered, the hacker used them for financial fraud and stealing confidential information.
On the other hand, Group-IB shared their report with Hackread.com that further explained how the company managed to identify five email addresses associated with the accused.
The cybersecurity firm was also successful in tracking six nicknames, and his accounts on different social media platforms including Facebook, Instagram, Skype, and Youtube.
According to Stephen…


