LockFile ransomware attacks Microsoft Exchange with ProxyShell exploits

A new ransomware gang known as LockFile encrypts Windows domains after hacking into Microsoft Exchange servers using the recently disclosed ProxyShell vulnerabilities.
ProxyShell is the name of an attack consisting of three chained Microsoft Exchange vulnerabilities that result in unauthenticated, remote code execution.
The three vulnerabilities were discovered by Devcore Principal Security Researcher Orange Tsai, who chained them together to take over a Microsoft Exchange server in April’s Pwn2Own 2021 hacking contest.
While Microsoft fully patched these vulnerabilities in May 2021, more technical details were recently disclosed, allowing security researchers and threat actors to reproduce the exploit.
As reported last week by BleepingComputer, this has led to threat actors actively scanning for and hacking Microsoft Exchange servers using the ProxyShell vulnerabilities.
After exploiting an Exchange server, the threat actors dropped web shells that could be used to upload other programs and execute them.
At the time, NCC Group’s vulnerability researcher Rich Warren told BleepingComputer that the web shells were being used to install a .NET backdoor that was downloading a harmless payload at the time.
Since then, security researcher Kevin Beaumont reports that a new ransomware operation known as LockFile uses the Microsoft Exchange ProxyShell and the Windows PetitPotam vulnerabilities to take over Windows domains and encrypt devices.
When breaching a network, the threat actors will first access the on-premise Microsoft Exchange server using the ProxyShell vulnerabilities. Once they gain a foothold, Symantec says the LockFile gang uses the PetitPotam vulnerability to take over a domain controller, and thus the Windows domain.
From there, it is trivial to deploy the ransomware through the entire network.
What we know about the LockFile ransomware
At this time, there is not much known about the new LockFile ransomware operation.
When first seen in July, the ransom note was named ‘LOCKFILE-README.hta‘ but did not have any particular branding, as shown below.
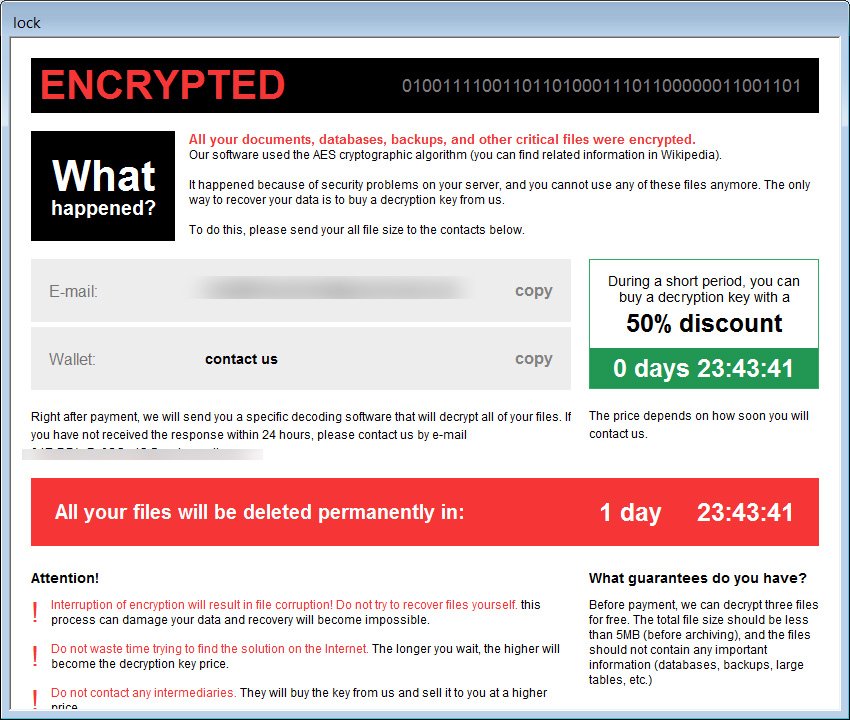
Starting last week, BleepingComputer began receiving reports of a ransomware gang…


