New ‘Morpheus’ CPU Design Defeats Hundreds of Hackers in DARPA Tests
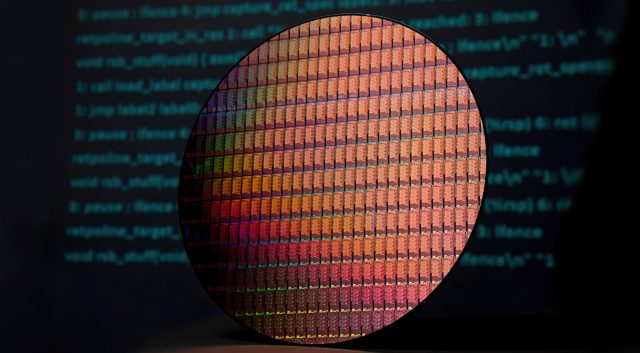
A new microprocessor design is being lauded for its security features after nearly 600 experts failed to hack it in a series of tests last summer. The new processor, codenamed “Morpheus,” continually rewrites its own architecture, making it impossible for an attacker to target the kinds of flaws that allow Spectre and Meltdown-style side-channel attacks against conventional x86 processors.
Morpheus was developed as part of a DARPA-funded project. Some 580 experts attempted to hack a medical database by injecting code into the underlying machine. Despite burning 13,000 hours collectively in an effort to hack the system, the effort failed.
“Today’s approach of eliminating security bugs one by one is a losing game,” said Todd Austin, professor of computer science and engineering at the University of Michigan. “People are constantly writing code, and as long as there is new code, there will be new bugs and security vulnerabilities…With MORPHEUS, even if a hacker finds a bug, the information needed to exploit it vanishes 50 milliseconds later. It’s perhaps the closest thing to a future-proof secure system.”

Morpheus was implemented using the gem5 simulator on a Xilinx FPGA and simulates a MinorCPU 4-stage in-order core running at 2.5GHz with a 32KB L1i and 32KB L1d. The L2 cache was 256KB. This is not a high-performance x86 CPU you can run out and buy, in other words.
According to Austin, his research team at the University of Michigan focused on making Morpheus a difficult target for any CPU-targeting exploit rather than focusing on building a chip that could defeat a specific class of exploits. The question was, how do you hide critical information from the attacker, without screwing up what the programmer is attempting to do — namely, write effective code?

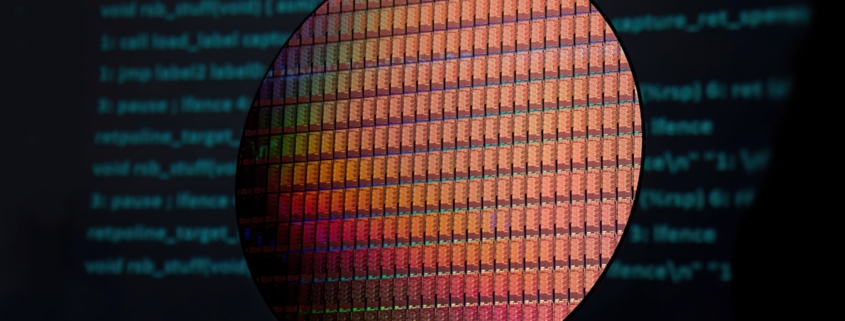
The Morpheus FPGA. Image credit: Todd Austin
Austin’s team settled on the idea of obfuscating a class…