Operationalize the NIST Cybersecurity Framework Without Pulling All Your Hair Out (Part 2 of 3)
This is the Part 2 of a 3-part blog on how to use the NIST cybersecurity framework without getting bogged down and lost in the minutia of the specification documents. Part 1 can be found here, and we recommend you read this piece first if you have not already done so.
Let’s recall the 5 core functions of NIST.
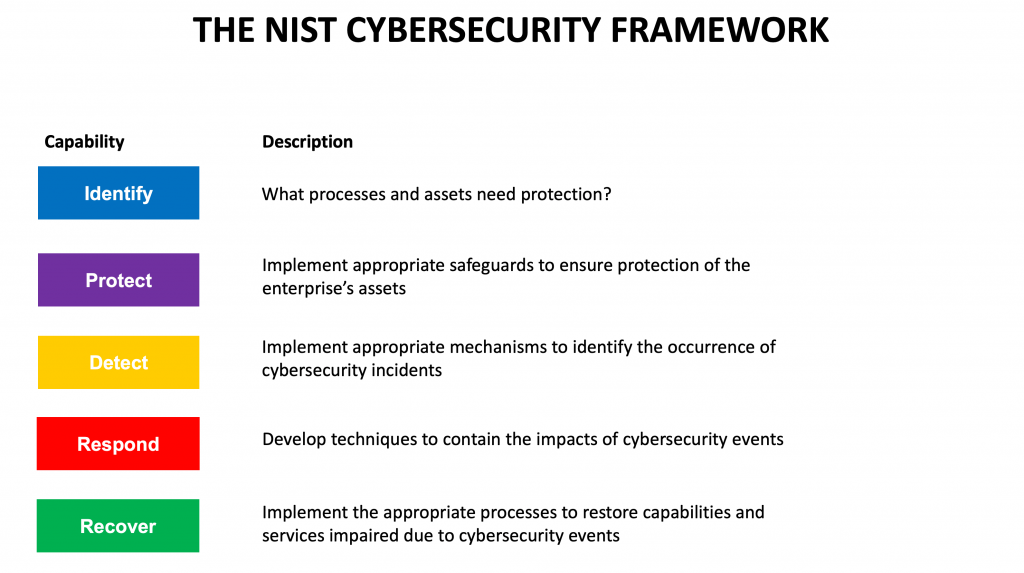
In Part 1 of this blog, we discussed the Identify function and how it is foundational to the NIST cybersecurity Framework. We saw how implementing Identify enables clear communication and decision-making within the cybersecurity team and in the board room.
We also discussed what you need to do in order to gain increased maturity in your implementation of Identify. We defined some KPIs that you can use everyday to track progress in the maturity level of your Identify capabilities.
In this 2nd part, we will discuss how to implement the Protect and Detect functions of the NIST cybersecurity framework.
PROTECT
“The key to protecting the enterprise is to be proactive in managing your vulnerabilities and risk items.”
Your 1st line of defense against cyberattacks consists of the following elements:
- Firewalls, IPSes, WAFs
- VPN and BeyondCorp
- Endpoint security
- Continuous vulnerability management
Firewalls allow you to implement a set of rules that restrict outside access to your internal network resources. In the old days all you needed to worry about was firewalls at the connection points between your various sites and the Internet. Today, you also need to worry about deploying and appropriately configuring firewalls at your cloud-based data centers (e.g., AWS VPCs), and for each mobile endpoint.
Intrusion Protection Systems (IPSes) inspect network traffic and block malicious network traffic, and may be deployed in addition to Firewalls or as part of a consolidated product. Web Application Firewalls are specialized systems designed to protect your public web-based applications.
Firewalls, IPSes and WAFs help you “lock down” access to your distributed enterprise. In order to support authorized users to securely access your network, Virtual Private Network (VPN) systems can be implemented. Some organizations, e.g., Google, have moved away from VPNs by…


