Subway marketing system hacked to send TrickBot malware emails
Subway UK has disclosed that a hacked system used for marketing campaigns is responsible for the malware-laden phishing emails sent to customers yesterday.
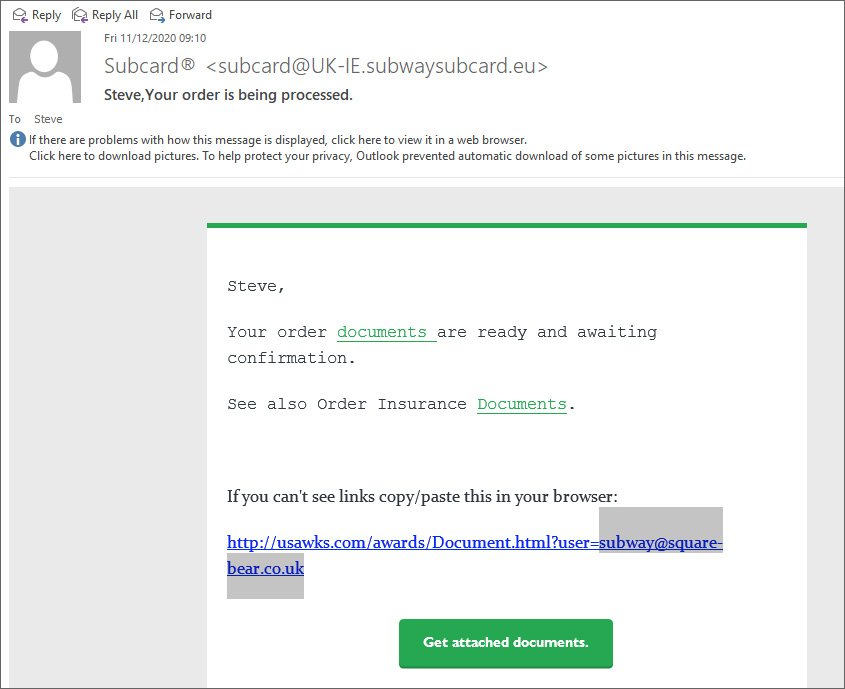
Starting yesterday, Subway UK customers received strange emails from ‘Subcard’ about a Subway order that was placed. Included in the email were links to documents allegedly containing confirmation of the order.
Source: Twitter
After analyzing these phishing emails, it was discovered that they were distributing malicious Excel documents that would install the latest version of the TrickBot malware.
TrickBot is a nasty malware infection that allows attackers to steal saved browser passwords, spread throughout a network, steal browser cookies, steal RDP, VNC, and PuTTY Credentials, and much more. Even worse, TrickBot may eventually provide access to the Ryuk or Conti ransomware operations.
As these emails contained a customer’s name and were using email addresses that some users created specifically for Subway, it caused suspicion that Subway had been breached somehow.
When we contacted Subway yesterday about this phishing campaign, we received a response that alluded to a ‘disruption’ of some sort on their email systems.
“We are aware of some disruption to our email systems and understand some of our guests have received an unauthorised email. We are currently investigating the matter and apologise for any inconvenience. As soon as we have more information, we will be in touch, until then, as a precautionary measure, we advise guests delete the email,” a Subway spokesperson told BleepingComputer.
Subway confirms a hacked server used in attack
After sending multiple emails to Subway about the ‘disruption’ seen on their system, the company disclosed that a server responsible for their email campaigns had been hacked to send out the phishing emails.
“Having investigated the matter, we have no evidence that guest accounts have been hacked. However, the system which manages our email campaigns has been compromised, leading to a phishing campaign that involved first name and email. The system does not hold any bank or credit card details.”
“Crisis protocol was initiated and compromised systems…


