BlackLotus Malware Bypasses Secure Boot on Windows Machines
Cybercrime
,
Endpoint Security
,
Fraud Management & Cybercrime
First in-the-Wild Bootkit Exploits Microsoft Vulnerability, Boots Up on Windows 11
Eset researchers discovered the first in-the-wild bootkit malware, called BlackLotus, bypassing security and booting up on fully up-to-date Windows 11 systems.
See Also: OnDemand | Navigating the Difficulties of Patching OT
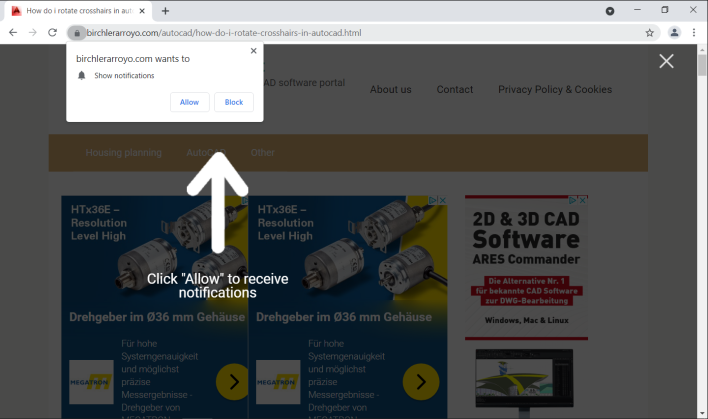
Security researchers found the Unified Extensible Firmware Interface bootkit in 2022 being sold on hacking forums for $5,000.
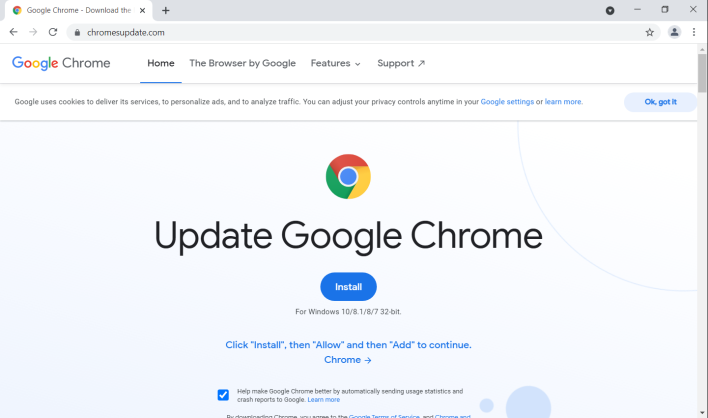
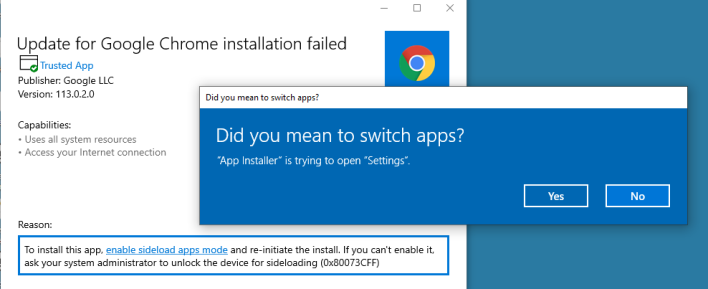
Secure Boot is the industry standard for ensuring only trusted operating systems can boot up a computer. BlackLotus malware can run on fully patched Windows 11 systems despite UEFI Secure Boot being enabled. It exploits a vulnerability that is more than 1 year old, tracked as CVE-2022-21894, to bypass UEFI Secure Boot and set up persistence for the bootkit.
Microsoft fixed this vulnerability in its January 2022 patch update, but BlackLotus adds vulnerable binaries to the system in order to exploit it.
A proof-of-concept exploit for this vulnerability has been publicly available since August 2022.
The malware can disable OS security mechanisms such as BitLocker, Hypervisor-Protected Code Integrity, and Windows Defender.
Martin Smolár, a malware analyst at Eset, says UEFI bootkits are very powerful threats. By by gaining complete control over the OS boot process, he says, threat actors can disable “various OS security mechanisms” by “deploying their own kernel-mode or user-mode payloads in early OS startup stages.”
This enables threat actors to operate stealthily…