Jackson County legislator’s email not connected to ransomware attack
KANSAS CITY, Mo. — An email sent from Jackson County Legislator Sean Smith was sent to roughly 50,000 voters on Friday.
The email is not related to the ransomware attack in Jackson County on Tuesday.
“It did not dawn on me that people would be concerned with its legitimacy because of the hacking issues that we had in Jackson County,” Smith said. “But yes, that’s me with a tool that we use at the county for email newsletters and stuff all the time. It’s all pretty safe and secure It’s absolutely separate from all of the county networks that we’ve had issues with.”
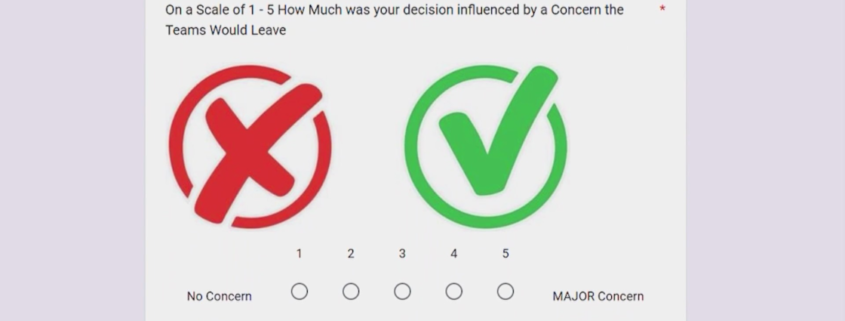
The email contains a link that leads to a survey. The survey asks voters how they voted on Tuesday’s “Question 1” and why they chose to vote that way.
“It’s a little weird. I don’t know why you’re sending out emails trying to figure out how people voted,” Broderick Jones said. “Whatever it was, it happened the way it happened, and that’s the way it is. Keep moving.”
Smith told FOX4 that he’s collecting the data because he’s “optimistic that we’ll eventually be in talks again with the teams and we need to understand what people’s concerns were in order to have any success going forward.” Leading up to the vote, Smith thought that the county was “not as ready as we’d like to be,” saying that the data will help him understand his constituency better. “Having data and information about why people have the preferences and concerns they have is the best way for me to represent them.”