Black Majority Schools Face Alarming Internet Security Risks, Report Finds
There is a large digital divide affecting low-income and Black or Indigenous majority schools, a recent report by Internet Safety Labs (ISL) has found.
Ads and trackers
The report “Demographic Analysis of App Safety, Website Safety, and School Technology Behaviors in US K-12 Schools” explores technological disparities in American schools, focusing mainly on marginalized demographics.
This research expands on ISL’s previous work on the safety of educational technology across the country and is supported by the Internet Society Foundation. It reveals how schools of different backgrounds use technology and the risks involved.
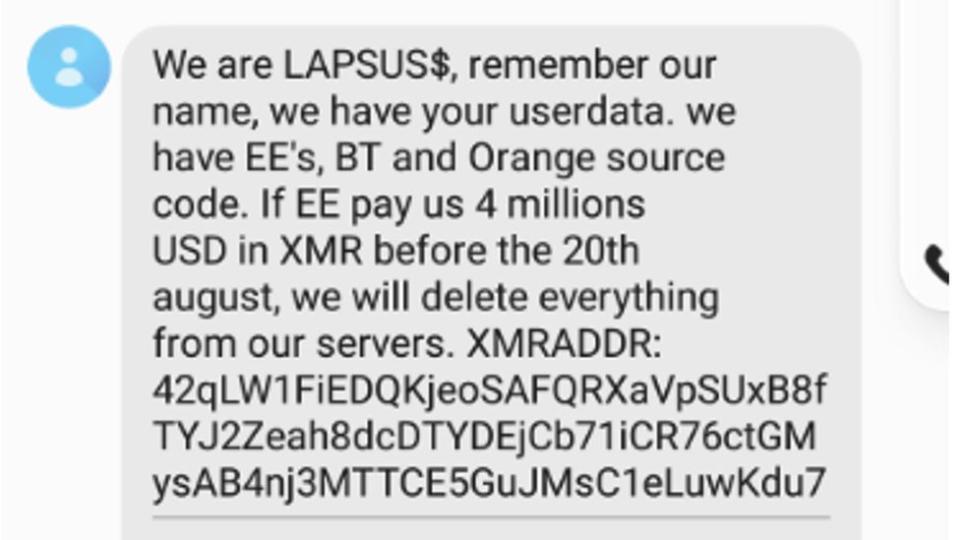
One concerning finding is that websites for schools with mostly Black students were the least safe.
One-third of these schools had advertisements on their websites—a rate much higher than the national average—and 100% of the websites had trackers monitoring visitor behavior.
Privacy or digital divide?
The study also highlights a broader problem: a digital divide in how technology is used in education.
Schools in the lowest income bracket, making between $20,000 and $39,000, were among the least likely to provide their students with computing devices. This limits these students’ experience with technology.
Furthermore, the technology that is recommended or required often poses privacy risks, including apps filled with digital and behavioral ads.
Similar trends were seen for schools with the most American Indian/Native Alaskan students, leading to concerns about how this digital divide impacts students’ learning and their understanding of technology.
What Is The Solution?
The report suggests several actions for schools, school districts, and policymakers.
It recommends eliminating digital ads and tracking devices on school websites.
It also emphasizes the importance of schools being transparent about the technology they use, suggesting they publish a comprehensive list of required technology so students and parents know what’s expected.
Finally, it suggests schools should thoroughly vet all technology they recommend or require for educational use, to ensure it’s safe and appropriate…