New Jersey Takes Stock of Cybersecurity Threats, Protections
There’s a cybersecurity concern that often doesn’t get enough attention, according to New Jersey CISO Michael Geraghty. That’s systemic cybersecurity risk, where an attack on one organization has effects that ripple out across the wider sector.
“Most of the time we think of, let’s say, a school system gets hit with ransomware, a system has to shut down, and it’s a localized incident,” said Geraghty, who is also director of the New Jersey Cybersecurity and Communications Integration Cell (NJCCIC).
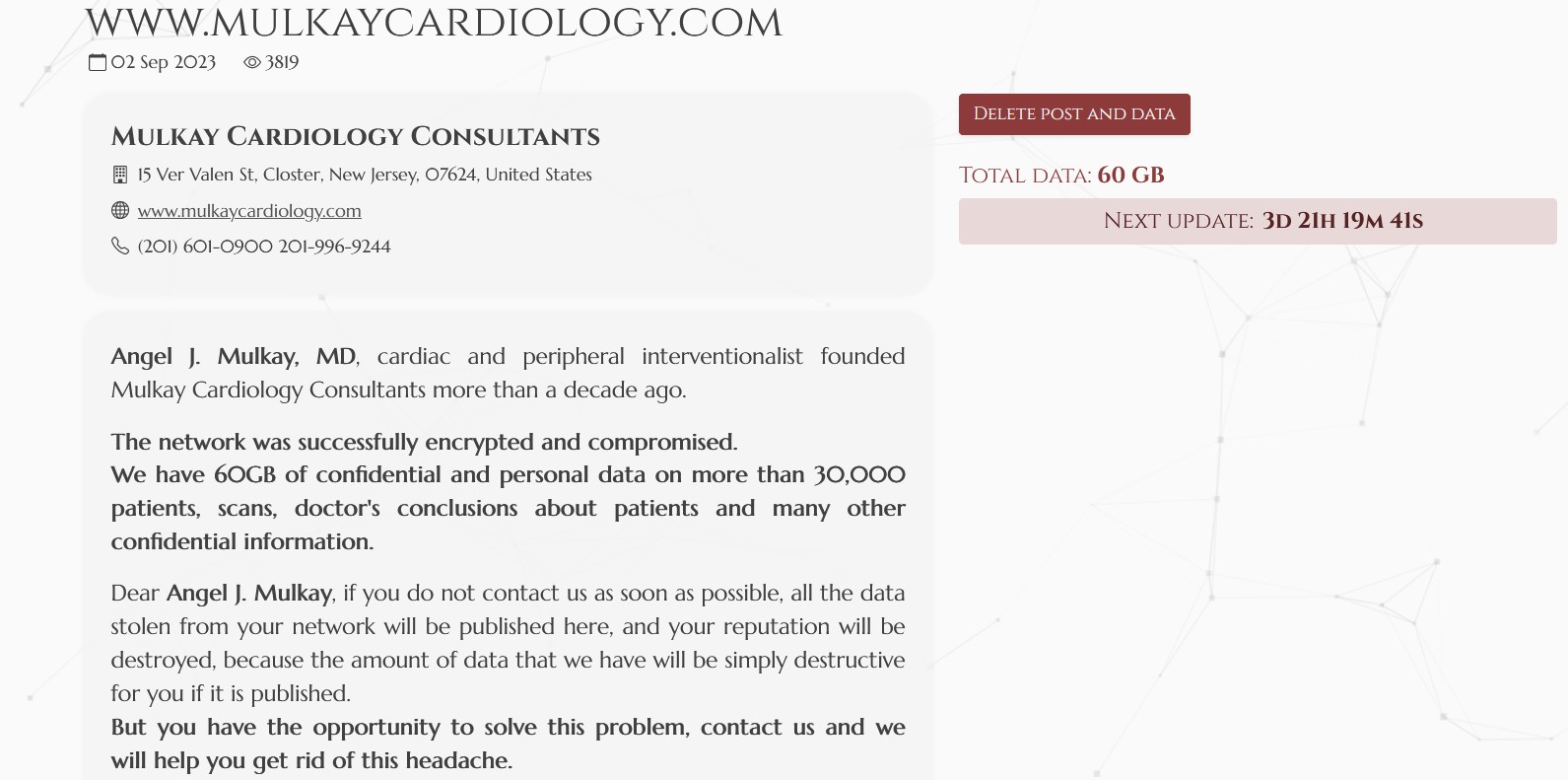
But attacks like the recent ransomware incident that disrupted Change Healthcare show just how hard systemic impacts can hit. Through that attack, actors were able to affect hospitals across the country.
“Here we have one organization — Change Healthcare — where it’s an individual organization that’s affecting the rest of the health-care system in the United States,” Geraghty said.
UnitedHealth Group’s Change Healthcare is a major medical claims processor. BlackCat ransomware struck the company, leading to a prolonged outage that left many hospitals and other health-care providers struggling to submit claims to insurance. Many have been running low on funds. The CEO of independent physician practices network Aledade told the Washington Post that about a quarter of U.S. physician practices are in severe financial distress.
Systemic risk is especially high in sectors where many players rely on the same vendor or technology. That’s what’s made Change Healthcare, MOVEit and Citrix Bleed nationwide events.
New Jersey organizations suffered from the latter two, with MOVEit compromising the personal info of more than 1 million residents, based on incidents reported to NJCCIC, per the state’s 2024 Threat Assessment report. And Citrix Bleed disrupted New Jersey hospitals, forcing problems ranging from slow patient care to postponed surgeries.
In contrast, election infrastructure is highly diversified, so a single attack would not have wide-scale impacts on election security, Geraghty said. He added that vendor and technology diversification is just one possible security approach, and that organizations…