Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking
A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors to execute arbitrary code and seize full control of vulnerable devices.
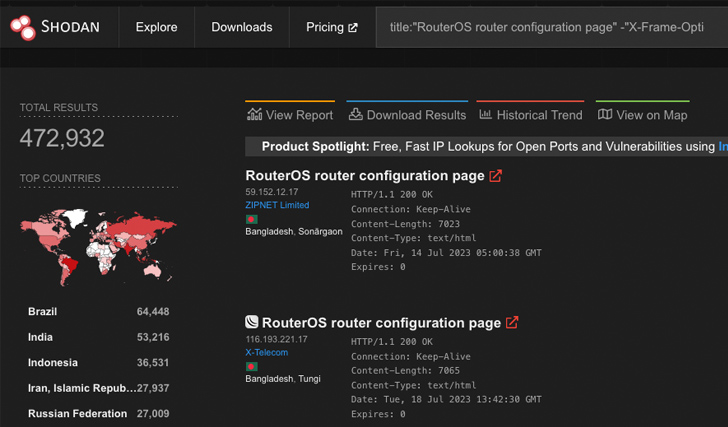
Cataloged as CVE-2023-30799 (CVSS score: 9.1), the shortcoming is expected to put approximately 500,000 and 900,000 RouterOS systems at risk of exploitation via their web and/or Winbox interfaces, respectively, VulnCheck disclosed in a Tuesday report.
“CVE-2023-30799 does require authentication,” security researcher Jacob Baines said. “In fact, the vulnerability itself is a simple privilege escalation from admin to ‘super-admin’ which results in access to an arbitrary function. Acquiring credentials to RouterOS systems is easier than one might expect.”
This is because the Mikrotik RouterOS operating system does not offer any protection against password brute-force attacks and ships with a well-known default “admin” user, with its password being an empty string until October 2021, at which point administrators were prompted to update the blank passwords with the release of RouterOS 6.49.
CVE-2023-30799 is said to have been originally disclosed by Margin Research as an exploit dubbed FOISted without an accompanying CVE identifier in June 2022. The security hole, however, was not plugged until October 13, 2022, in the RouterOS stable version 6.49.7 and on July 19, 2023, for the RouterOS Long-term version 6.49.8.
VulnCheck noted that a patch for the Long-term release tree was made available only after it directly contacted the vendor and “published new exploits that attacked a wider range of MikroTik hardware.”
A proof-of-concept (PoC) devised by the company shows that it’s possible to derive a new MIPS architecture-based exploit chain from FOISted and obtain a root shell on the router.
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
“Given RouterOS’ long history of…