What Tens of Thousands of Machines Witness
Disclaimer: This article is meant to give insight into cyber threats as seen by the community of users of CrowdSec.
What can tens of thousands of machines tell us about illegal hacker activities?
Do you remember that scene in Batman – The Dark Knight, where Batman uses a system that aggregates active sound data from countless mobile phones to create a meta sonar feed of what is going on at any given place?
It is an interesting analogy with what we do at CrowdSec. By aggregating intrusion signals from our community, we can offer a clear picture of what is going on in terms of illegal hacking in the world.
After 2 years of activity and analyzing 1 million intrusion signals daily from tens of thousands of users in 160 countries, we start having an accurate “Batman sonar” global feed of cyber threats. And there are some interesting takeaways to outline.
A cyber threat with many faces
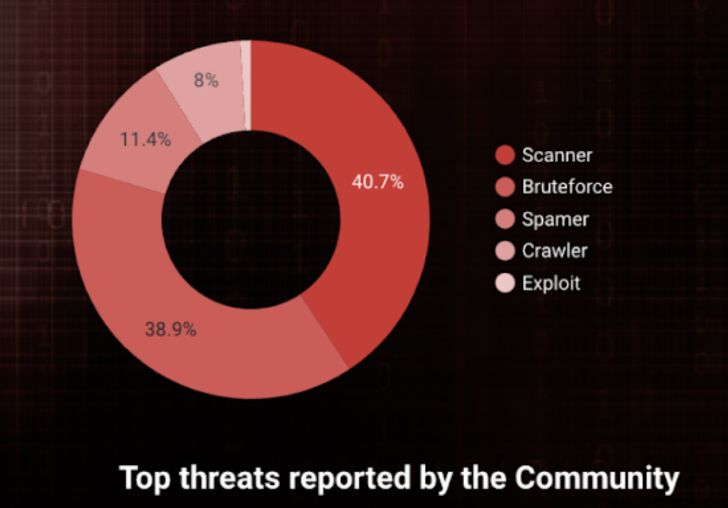
First of all, the global cyber threat is highly versatile. What do we see when looking at the types of attacks reported, their origin, and the Autonomous Systems (AS) behind the malicious IP addresses?
Scanners and Brute force attempts are still the most popular intrusion vectors our community sees and rank #1. Pretty logic, as surveillance is the first step to a more advanced intrusion. The scanning activities seen by our community are mostly port scans or HTTP-based probings.
Amongst the different intrusion types used by hackers, brute force attempts on sensitive services (SSH, email, admin URLs, etc.) is #2. Not breakthrough information, but when studies show that brute force attacks are accounted for 6% of cyber attacks in the world, it is not surprising to see it as dominant, especially since it is still one of the easiest and cheapest ones to automate and deploy (hello script kiddies). Because it is pretty easy to counter, one would think it rarely works, but hey, 6%!
Log4J is still not yet a done deal
Amongst the most popular exploit attempts our community sees, we have Log4j. You indeed enjoyed last year’s storm on how a simple open-source logging utility for Apache with a vulnerability took over the cybersecurity world and caused endless headaches to cybersecurity experts. And, of course,…