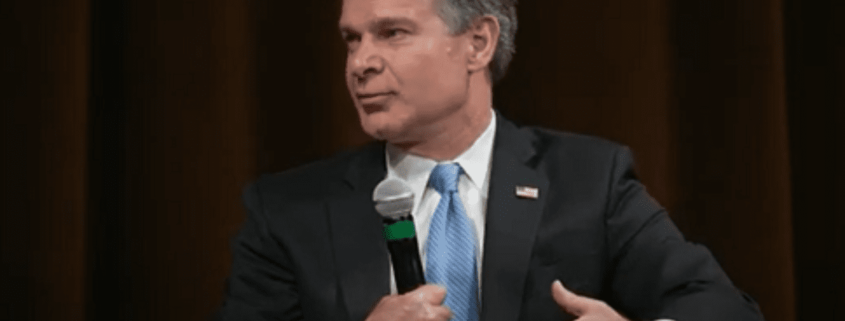
FBI’s Chris Wray warns Chinese hackers preparing to attack US infrastructure ‘to induce panic’
FBI Director Christopher Wray warned Thursday that a hacking group linked to the Chinese government is waiting for the right moment to “deal a devastating blow” to U.S. critical infrastructure.
Wray delivered a keynote speech at the Vanderbilt Summit on Modern Conflict and Emerging Threats in Nashville, and told national security and intelligence experts that the risks posed by the government of China to U.S. national and economic security are “upon us now.”
The director said a recent bureau investigation found that the Chinese government had gained illicit access to networks within America’s “critical telecommunications, energy, water, and other infrastructure sectors.”
“The PRC [People’s Republic of China] has made it clear that it considers every sector that makes our society run as fair game in its bid to dominate on the world stage, and that its plan is to land low blows against civilian infrastructure to try to induce panic and break America’s will to resist,” Wray said — the FBI explained “these vital sectors—everything from water treatment facilities and energy grids to transportation and information technology—form the backbone of our society.”
“The fact is, the PRC’s targeting of our critical infrastructure is both broad and unrelenting,” he added. “It’s using that mass, those numbers, to give itself the ability to physically wreak havoc on our critical infrastructure at a time of its choosing,”
Wray said CCP-sponsored cyber actors “prepositioned” themselves to potentially mount cyber offenses against American energy companies in 2011—targeting 23 different pipeline operators, with Wray saying this helps understand current motivations.
“When one victim company set up a honeypot—essentially, a trap designed to look like a legitimate part of a computer network with decoy documents—it took the hackers all of 15 minutes to steal data related to the control and monitoring systems, while ignoring financial and business-related information, which suggests their goals were even more sinister than stealing a leg up economically,” he said.
The CCP also targeted critical infrastructure organizations through more…