Window opens for new internet security section
Stacy Shi
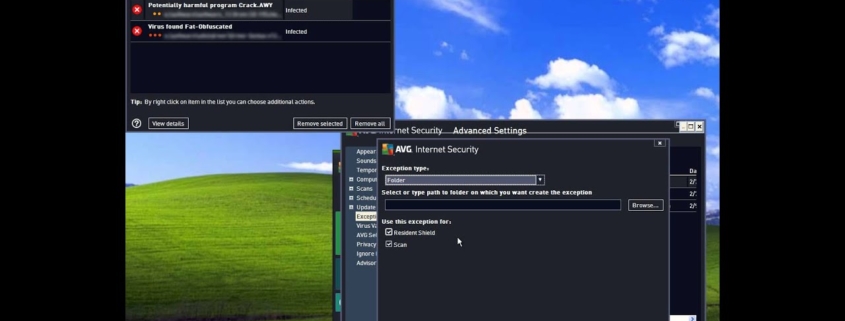
A new department may be created under the Digital Policy Office to oversee internet security and manage major digital projects, Secretary for Innovation, Technology and Industry Sun Dong told the Legislative Council yesterday.
Sun was replying to lawmaker Yung Hoi-yan’s concerns over system failures in recent months, including the suspension of voting for last year’s district council election at polling stations.
”To support the important mission of building a digital government in the future, the government is formulating new policies, with a view to strengthening the future Digital Policy Office, at different work junctures such as project initiation, tendering, formulation of technical options, system development, testing and risk assessment,” Sun said.
The policies are aimed at providing greater support to bureaus and departments and enhancing the stability and security of government e-services, he added.
On the electronic poll register system failure in December, Sun said the Registration and Electoral Office conducted three levels of monitoring and testing for the system and the Electoral Affairs Commission is investigating the causes to ensure it will not recur.
”The findings will be reported in detail in the report to be submitted to [Chief Executive John Lee Ka-chiu] within three months after the election as required by law.”
Election Committee sector lawmaker Priscilla Leung Mei-fun said she was upset to see some voters being unable to cast their ballot, asking whether there will be backup plans or mainland experts imported to avoid similar incidents in the future.
”We have immediately switched to printed copies of the voter register to issue ballot papers, which was among our backup plans,” Secretary for Constitutional and Mainland Affairs Erick Tsang Kwok-wai said. “We will further enhance the training of our colleagues in this respect, and arrange for relevant rehearsals.”
In addition, Sun said the Office of the Government Chief Information Officer has already rolled out an enforcement guideline on supervising contractors in a bid to solve recent mishaps in the government’s IT system.
He said…