The DeanBeat: Twitch hack exposes more industry secrets
Join gaming leaders online at GamesBeat Summit Next this upcoming November 9-10. Learn more about what comes next.
Perhaps the lesson of the leak of a trove Twitch‘s data, source code, and internal tools is that we can expect this to happen to just about everybody in the industry. And one of these days, perhaps we won’t have any secrets left.
This week, hackers disclosed that they had penetrated Twitch’s security and had access to just about all of its secrets and they would disclose those secrets. We don’t know if they’re trying to extract blackmail payments from Twitch, but that might be a logical assumption.
Among the secrets that leaked was a list of how much money the top streamers on the livestreaming service made in subscription revenue.
The list showed that 81 Twitch streamers have made more than $1 million on Twitch since August 2019. At the top was Critical Role, a team of voice actors who stream their Dungeons & Dragons gameplay. They made $9.6 million from Twitch payments in the past two years. Making more than $5 million since August 2019 was FaZe Clan co-owner and Call of Duty streamer Nickmercs. All of the top 25 made more than $2 million each over the two years. The BBC reported that a few streamers confirmed that the figures are accurate.
Webinar
Three top investment pros open up about what it takes to get your video game funded.
Watch On Demand
This doesn’t include the money the streamers make on other platforms such as YouTube or how much they make with merchandise sales, sponsorships, and external donations. But the leak did reveal that Twitch takes a 50% share of creator earnings. That’s a pretty big cut considering those creators bring in the 2.5 million concurrent users to Twitch every day.

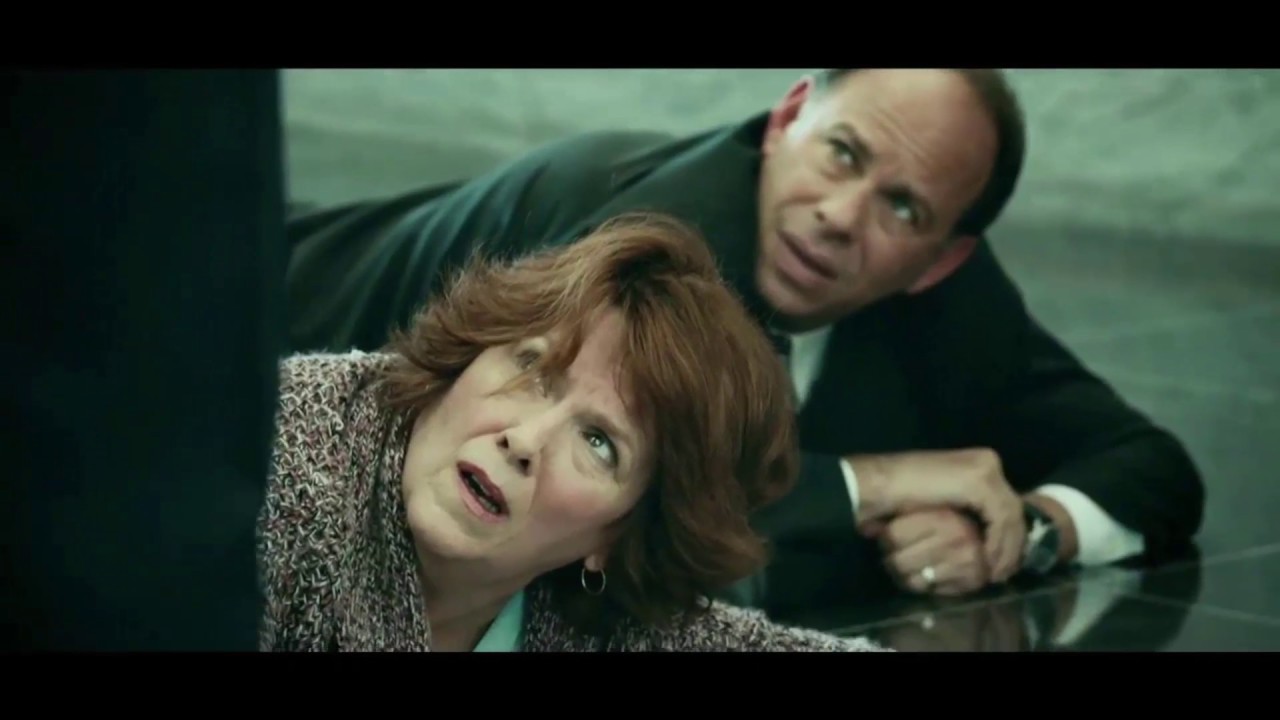
Above: Hackers, whistleblowers, and ransomware thieves seem like they are winning.
Image Credit: Getty Images
Twitch confirmed the hack was real. It said the data was exposed to the internet due to an error in a Twitch server configuration change that was subsequently accessed by a malicious third party….