The Navy Wants You To Hack Into Its Systems. Here’s Why
In the 1983 movie WarGames, a young Matthew Broderick plays a high school-age hacker who unwittingly breaks into a United States military supercomputer from his bedroom. Broderick’s character thinks he’s found some unreleased computer games to play, with promising titles like “Global Thermonuclear War” and “Theaterwide Biotoxic and Chemical Warfare.” In reality, he’s accessed a war-simulation program that comes close to bringing about a conflict with the Soviet Union that would result in mutually assured nuclear annihilation.
Jump forward the best part of 40 years, and users can take a turn at this for themselves (well, kind of) — and it’s thanks, in part, to a man named Zac Staples. Staples spent 22 years serving his country in the United States Navy as a surface officer with a special interest in cyberwarfare. He retired in December 2017, took exactly two days off, then started a tech company called Fathom5. The Austin, Texas-based company’s website describes its line of work as “building secure pipelines and tools for industrial technology applications while reducing cyber vulnerability.”
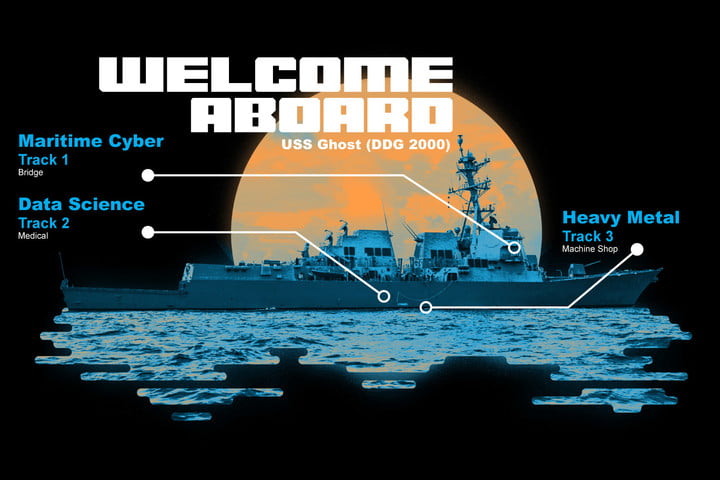
With the approval and funding of the U.S. Navy, Fathom5 launched a hackathon called HACKtheMACHINE, an event that seeks to give lone hackers and small startups the ability to compete for prize money and military contracts by, among other things, hacking naval infrastructure.
“When you look at [the cybersecurity landscape today], you have Advanced Persistent Threats — APT — which is kind of like cyber community speak for Russian and Chinese hacking that’s state-funded,” Staples told Digital Trends. “These are potential competitors in the global landscape who are actively funding offensive cyber teams. We have to be proactively thinking about how we’re going to defend against that. We’ve seen Russia use cyber as a precursor to kinetic operations a couple of times, including the invasion of Ukraine [and] Crimea. I don’t think there’s been a future battle that doesn’t either begin with cyber or is enabled by cyber, even if it’s just as a way to conduct espionage.”
Bug bounty for the Navy
Many tech companies today have what are called…


