WAPDropper Android Malware Targets Southeast Asia Users, Experts Warn
Security firm Check Point discovers a new malware called WAPDropper that spreads through malicious apps and targets users in Southeast Asia.
The malware victims are charged for expensive premium mobile services once they downloaded the apps. The attack is similar to the ones that became popular in the late 2000s.

(Photo : Jonah Pettrich/Unsplash)
WAPDropper Malware
How WAPDropper Malware works?
Check Point security researchers said the new Android malware are acquired using malicious apps from third-party app stores. Once the malware gets through, it signs up users for premium phone numbers, which charge huge fees for different services. Meanwhile, a CAPTCHA step is sometimes required to finalize the subscription.
This results to large phone bills every month until they contact their mobile provider to file a report about the issue or unsubscribe from the premium number.
This kind of attack became popular in the late 2000s, but vanished later as smartphones came out. However, it managed to return in the early 2010s after cyberattackers found that there are numerous telephone companies and modern phones that still used the older WAP standard.
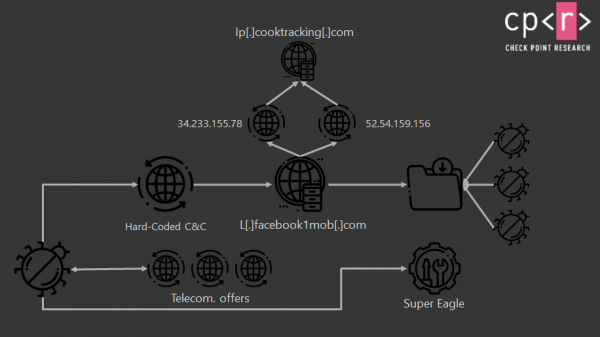
(Photo : Check Point)
WAPDropper Malware: Security Researchers Discovers Mobile Malware Targeting Southeast Asia Users
According to Check Point, the WAPDropper operated using two modules: the dropper and the component that implemented the actual WAP fraud.
The first module was packed inside the malicious apps, which reduces the fingerprint and size of malicious code. Once victims downloaded these apps and installed them on the device, the module would download the second component, which would begin swindling the users.
Read also: Cybercriminals Now Target Google Workspace Tools: 5 Phishing Campaigns Use Form, Docs, and Sites
WAPDropper Malware attackers from Southeast Asia
Check Point researchers claim that upon checking the premium phone numbers that were used in this malware scheme, the cybercriminals are likely to be from Malaysia or Thailand. It is also possible that they are working with people from these countries.
Researchers said the attack is a numbers game, in which more revenue is…

