Why Understanding Cyber Criminals Behavior and Tools is Vital
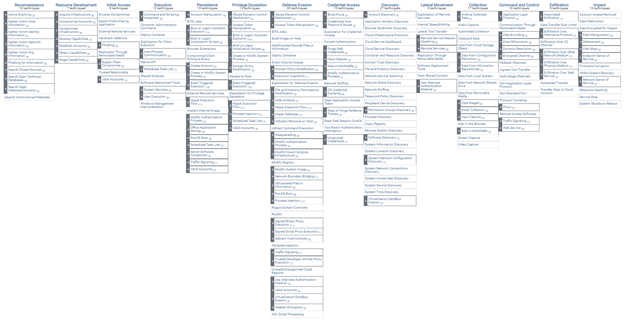
The attack landscape continues to grow rapidly, and with that growth comes the complex challenge of tracking the Tactics, Techniques, and Procedures (TTPs) used by different threat actors. The National Institute of Standards and Technology’s (NIST) Computer Security Resource Center describes TTPs as the behavior of a threat actor; tracking that behavior has become an essential concept for Cyber Threat Intelligence (CTI) Analysts. By profiling and documenting criminal TTPs network defenders can better understand criminal behavior and how specific attacks are orchestrated, allowing them the ability to prepare, respond and mitigate current and future threats.
Defining Tactics, Techniques, and Procedures
To further break down TTP, Tactics refer to the high-level descriptions of the behavior or action the threat actor is trying to accomplish. For example, Initial Access is a tactic a threat actor would leverage to gain a foothold into your network.
Techniques are detailed descriptions of the behavior or actions that are expected from a specific Tactic. For example, a Technique to gain Initial Access to a network could include a phishing attack.
Procedures are technical details or directions about how a threat actor will leverage the Technique to accomplish their objective. For example, the Procedures for a phishing attack would include the order of operation or phases of the campaign. This would include details about the infrastructure leveraged to send the malicious email, whom they plan to target and how they plan on compromising their machine.
Unfortunately, tracking the behaviors of threat actors has been a complex challenge for our industry, mainly because we did not have a single and universally adopted, standardized framework to adhere to. As mentioned in part 1 of our Hackers Almanac series, depending on the security organization who is attributing a digital attack, a threat group known as APT10 by Mandiant also goes by: menuPass by Fireeye, Stone Panda by Crowdstrike, or Red Apollo, Cloud Hopper and POTASSIUM by Microsoft. Making documenting, reporting, and speaking about threat actors extremely difficult.
Fortunately, over the last few years, the industry has begun to…