YouTube Account Hacked? New 2FA-Bypass YTStealer Attacks Are Underway
YouTube creators warned of automated account takeover attacks
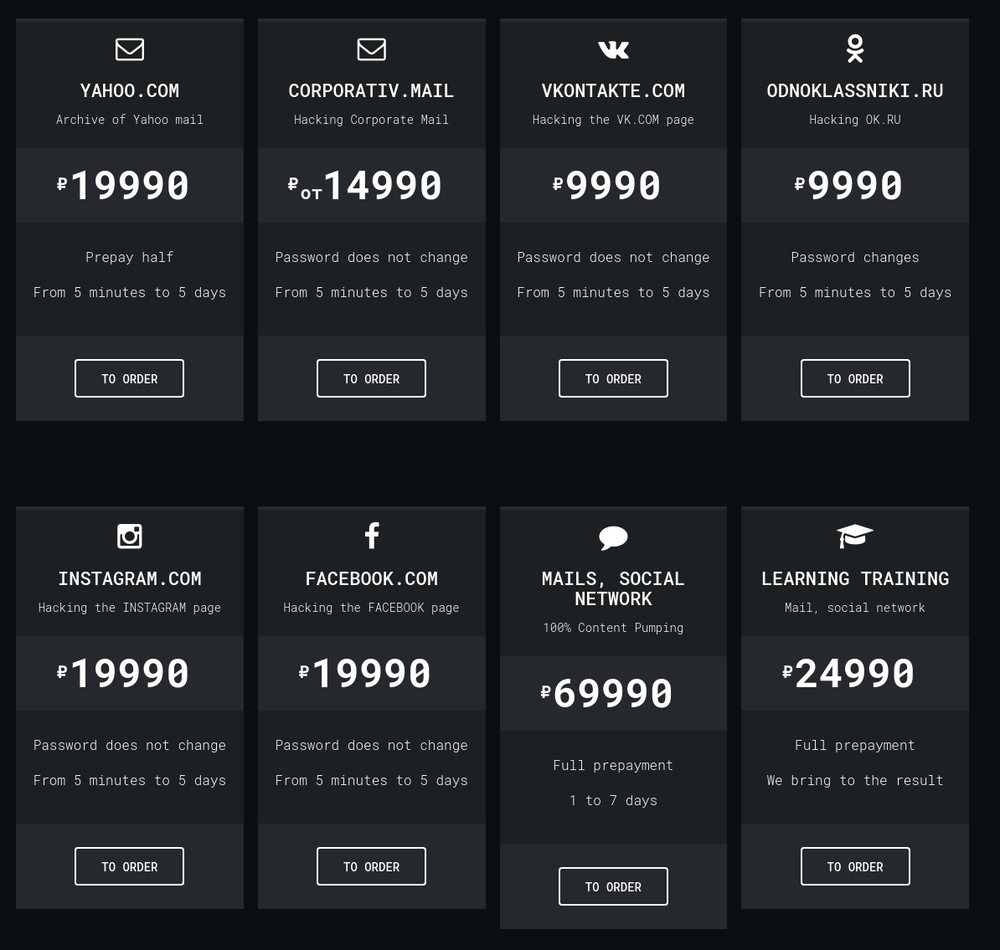
When it comes to credential theft and account takeovers, you might think that cybercriminals are somewhat indifferent as to what account is compromised. This is true, to a degree. Some accounts are more valuable than others, an email account can hold the keys to various kingdoms for example, but any account hack is a win. Where specialization is a factor, and a profitable one at that, is within the assorted online forums where malware to attack specific account types is sold.
When the accounts in question are those belonging to YouTube creators, given the number of eyes these can attract, then it grabs my attention. Particularly when in the case of YTStealer it can effectively bypass 2FA protections. With YTStealer being sold as a service to cybercriminals, it should come as no surprise that security researchers have spotted fully automated YTStealer attacks underway with compromised accounts already being sold on the dark web.
According to a report from automated security intelligence provider Intezer, YTStealer is “malware whose objective is to steal YouTube authentication cookies.” A credential harvester focused entirely on gaining control of YouTube creator accounts, be they of ‘influencer’ follower proportions or small fishes in this incredibly large content creation sea. Once this account compromise as a service malware has harvested the credentials, it’s up to the customer what they do with them: high-value accounts could be sold at profit or compromised in order to spam or spread further malware.
How does a YTStealer attack work?
Then Intezer report discovered that game mods and trainers, or cheats if you prefer, were one of the target groups where YTStealer was dropped in the guise of an installer or a genuine application. These included various hacks for Counter-Strike Go, Call of Duty, and Roblox. Unsurprisingly, audio and video editing was another, with fake installers for the likes of Adobe Premiere Pro and Ableton Live 11 Suite among them. There were also other…