Vulnerability Exploits Triple as Initial Access Point for Breaches
The exploitation of vulnerabilities as an initial access step for a breach increased by a staggering 180% between 2022 and 2023.
According to Verizon’s 2024 Data Breach Investigations Report (DBIR), published on May 1, this method of gaining unauthorized access leading to a breach accounted for 14% of malicious actors’ way into a network. It is the third most used after credential theft and phishing.
This growth is partly due to the exploitation of the MOVEit vulnerability and several other zero-day exploits that ransomware actors used throughout 2024, the report said.
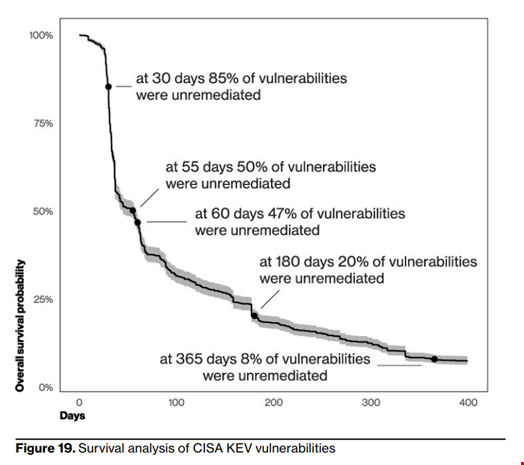
“It is truly concerning. Even when considering only the US Cybersecurity Infrastructure and Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) catalog, it takes organizations around 55 days to remediate 50% of those critical vulnerabilities after their patches are available – a dangerous lag,” warned Verizon.
“On the flip side, the median time for detecting the first scan for a CISA KEV vulnerability is five days from publication in the Common Vulnerabilities and Exposures (CVE) database (not from the patch being available).”
This exploitation of these vulnerabilities also comes at a critical moment for the software security community. Recently, the US National Institute of Standards and Technology struggled to keep the National Vulnerability Database (NVD) afloat, marred by resource and financial issues.
The NVD is the most used vulnerability repository worldwide. It lists reported CVEs and provides metadata that helps mitigate the risk associated with them. However, the NVD program has experienced a serious backlog of vulnerability enrichment since February 2024.
Read more: NIST Unveils New Consortium to Operate National Vulnerability Database
With the prevalence of vulnerability exploits, Verizon started monitoring software supply chain attacks, which rose by 68% in 2023 compared to 2022.
In total, 15% of breaches involved a third party, including data custodians or hosting partners being breached and direct or indirect software supply chain issues.
Stolen Credential, Top Initial Access Method
Stolen credentials remain…


