3 Ransomware Group Newcomers to Watch in 2024
The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 4,368 cases.
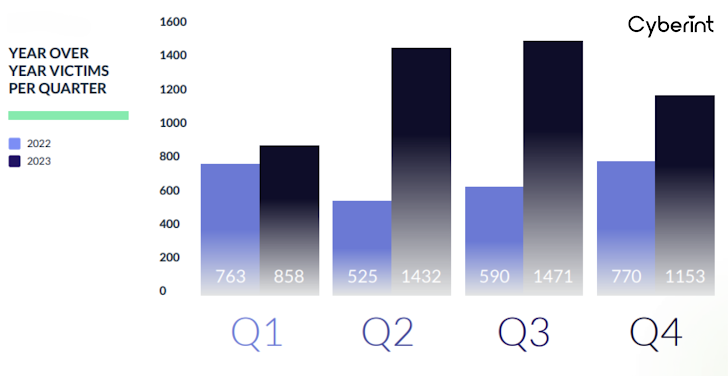 |
| Figure 1: Year over year victims per quarter |
The rollercoaster ride from explosive growth in 2021 to a momentary dip in 2022 was just a teaser—2023 roared back with the same fervor as 2021, propelling existing groups and ushering in a wave of formidable newcomers.
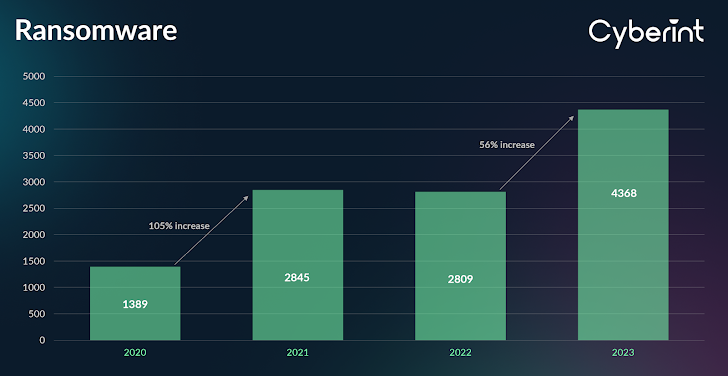 |
| Figure 2: 2020-2023 ransomware victim count |
LockBit 3.0 maintained its number one spot with 1047 victims achieved through the Boeing attack, the Royal Mail Attack, and more. Alphv and Cl0p achieved far less success, with 445 and 384 victims attributed to them, respectively, in 2023.
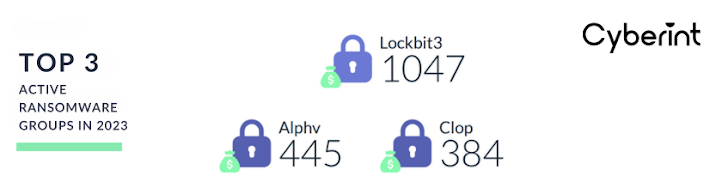 |
| Figure 3: Top 3 active ransomware groups in 2023 |
These 3 groups were heavy contributors to the boom in ransomware attacks in 2023, but they were not the sole groups responsible. Many attacks came from emerging ransomware gangs such as 8Base, Rhysida, 3AM, Malaslocker, BianLian, Play, Akira, and others.
Newcomers to the Ransomware Industry
At Cyberint, the research team is constantly researching the latest ransomware groups and analyzing them for potential impact. This blog will look at 3 new players in the industry, examine their impact in 2023 and delve into their TTPs.
To learn about other new players download the 2023 Ransomware Report here.
3AM Ransomware
A newly discovered ransomware strain named 3AM has emerged, but its usage has been limited so far. In 2023 they have only managed to impact 20+ organizations (mostly in the USA). However, they are gaining notoriety due to a ransomware affiliate who tried to deploy LockBit on a target’s network switching to 3AM when LockBit was blocked.
New ransomware families appear frequently, and most disappear just as quickly or never manage to gain significant traction. However, the fact that 3AM was used as a fallback by a LockBit affiliate suggests that it may be of interest to attackers and could be seen again in the future.
Interestingly, 3AM is coded in Rust and appears to be an entirely new malware family. It follows a specific sequence: it attempts to halt multiple services on the compromised computer before initiating the file encryption process. After…


