Androxgh0st Malware Botnet Steals AWS, Microsoft Credentials and More
The Federal Bureau of Investigation and Cybersecurity & Infrastructure Security Agency warned in a joint advisory about a threat actor deploying a botnet that makes use of the Androxgh0st malware. This malware is capable of collecting cloud credentials, such as those from AWS or Microsoft Azure and more, abusing the Simple Mail Transfer Protocol, and scanning for Amazon Simple Email Service parameters.
What is the Androxgh0st malware?
The Androxgh0st malware was exposed in December 2022 by Lacework, a cloud security company. The malware is written in Python and is primarily used to steal Laravel.env files, which contain secrets such as credentials for high-profile applications. For instance, organizations can integrate applications and platforms such as AWS, Microsoft Office 365, SendGrid or Twilio to the Laravel framework, with all of the applications’ secrets being stored in the .env file.
The botnet hunts for websites using the Laravel web application framework before determining if the domain’s root level .env file is exposed and contains data for accessing additional services. The data in the .env file might be usernames, passwords, tokens or other credentials.
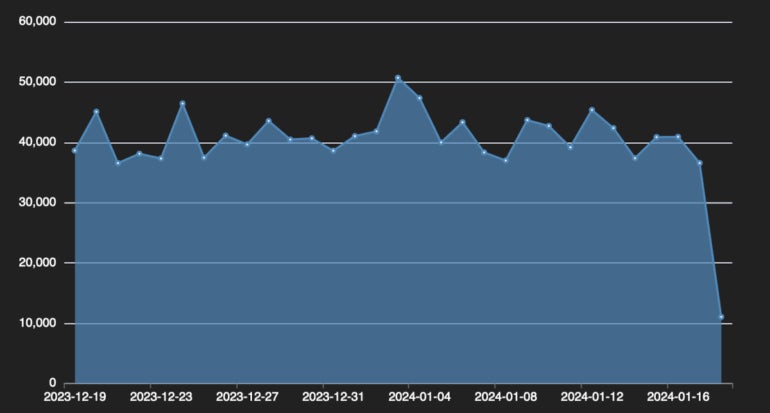
The cybersecurity company Fortinet exposed telemetry on Androxgh0st, which shows more than 40,000 devices infected by the botnet (Figure A).
Figure A
The FBI/CISA advisory states: “Androxgh0st malware also supports numerous functions capable of abusing the Simple Mail Transfer Protocol (SMTP), such as scanning and exploiting exposed credentials and application programming interfaces (APIs), and web shell deployment.”
How can Androxgh0st malware exploit old vulnerabilities?
In addition, Androxgh0st can access the Laravel application key; if that key is exposed and accessible, the attackers will try to use it to encrypt PHP code that is passed to the website as a value for the XSRF-TOKEN variable. This is an attempt to exploit the CVE-2018-15133 vulnerability in some versions of the Laravel web application framework. A successful attempt allows the attacker to remotely upload files to the website. CISA added the CVE-2018-15133 Laravel…