China-linked APT Volt Typhoon linked to KV-Botnet
China-linked APT Volt Typhoon linked to KV-Botnet
Researchers linked a sophisticated botnet, tracked as KV-Botnet, to the operation of the China-linked threat actor Volt Typhoon.
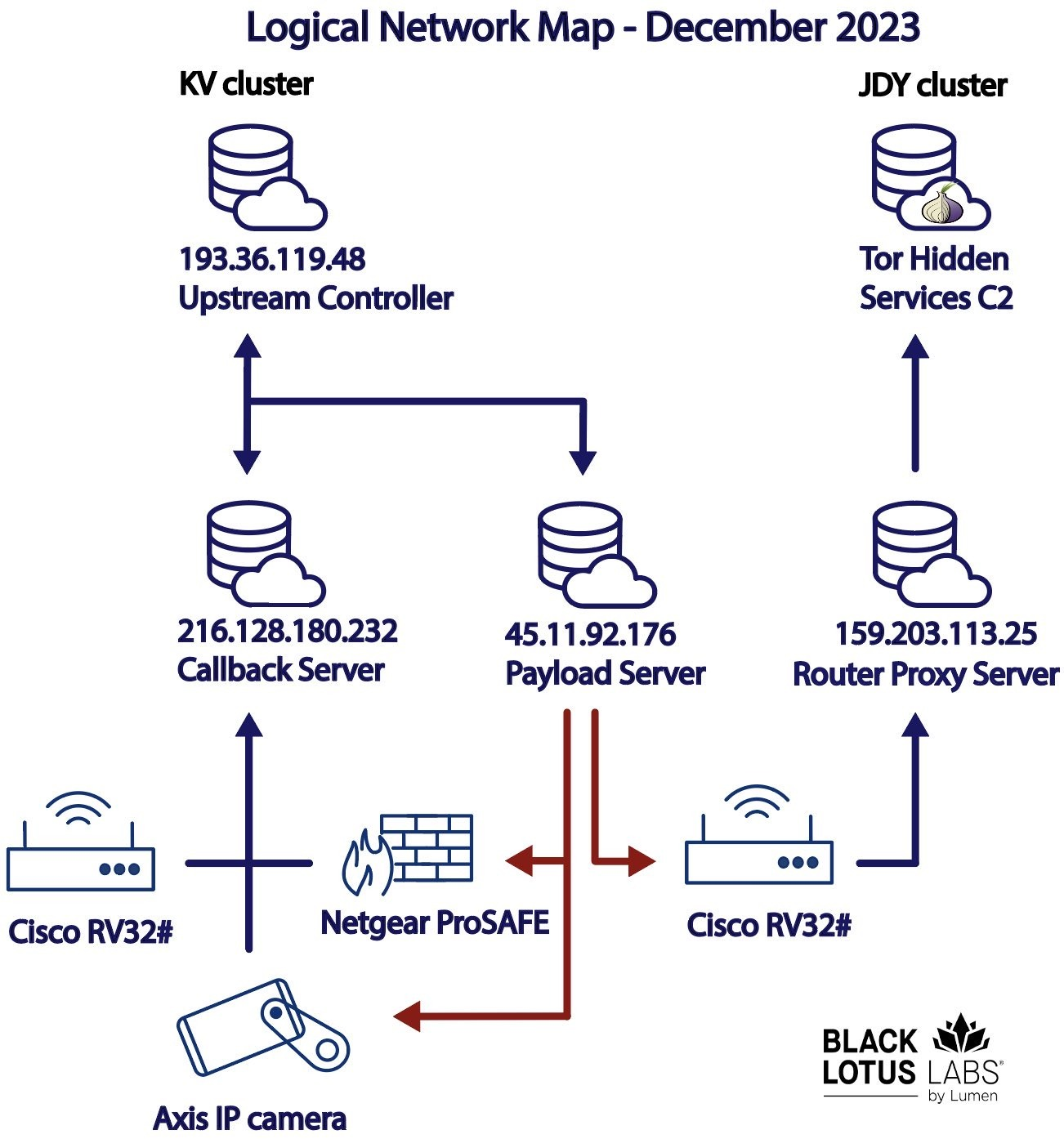
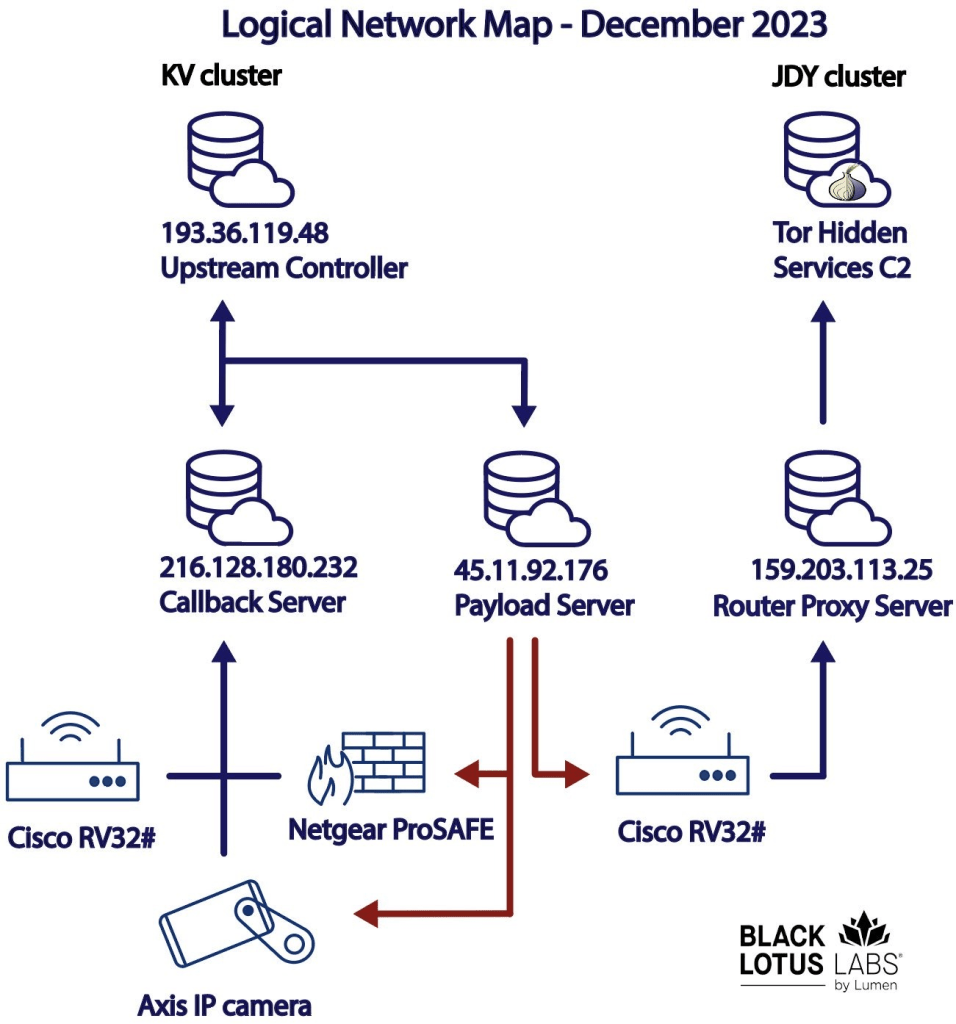
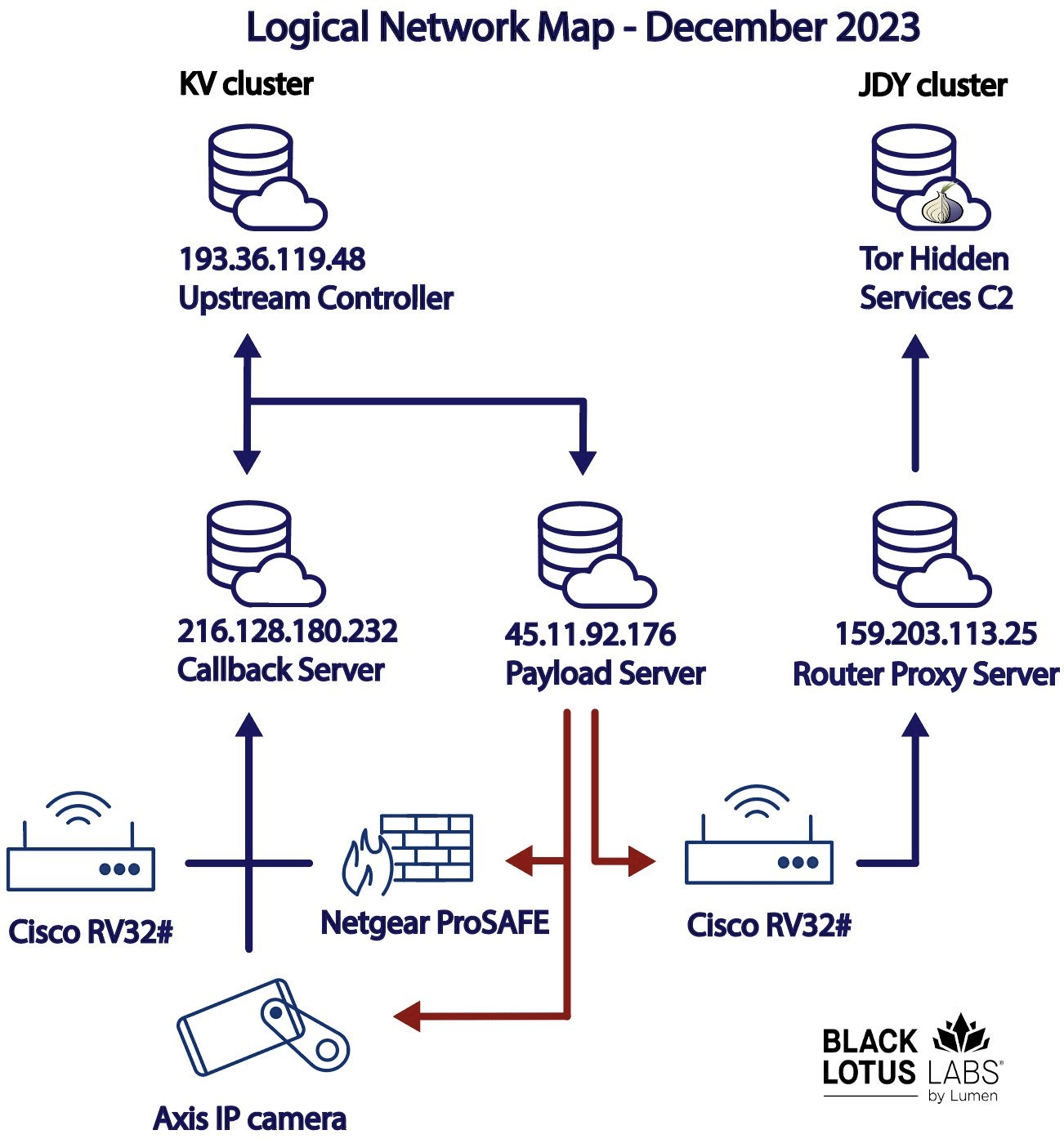
The Black Lotus Labs team at Lumen Technologies linked a small office/home office (SOHO) router botnet, tracked as KV-Botnet to the operations of China-linked threat actor Volt Typhoon. The botnet is comprised of two complementary activity clusters, the experts believe it has been active since at least February 2022. The threat actors target devices at the edge of networks.
The KV-Botnet is composed of end-of-life products used by SOHO devices. In early July and August of 2022, the researchers noticed several Cisco RV320s, DrayTek Vigor routers, and NETGEAR ProSAFEs that were part of the botnet. Later, in November 2022, most of the devices composing the botnet were ProSAFE devices, and a smaller number of DrayTek routers. In November 2023, the experts noticed that the botnet started targeting Axis IP cameras, such as the M1045-LW, M1065-LW, and p1367-E.
In May, Microsoft reported that the Volt Typhoon APT infiltrated critical infrastructure organizations in the U.S. and Guam without being detected. The group managed to maintain access without being detected for as long as possible.
According to Microsoft, the campaign aimed at building capabilities that could disrupt critical communications infrastructure between the United States and Asia region in the case of future crises.
The Volt Typhoon group has been active since at least mid-2021 it carried out cyber operations against critical infrastructure. In the most recent campaign, the group targeted organizations in the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors.
The APT group is using almost exclusively living-off-the-land techniques and hands-on-keyboard activity to evade detection.
Microsoft first noticed that to conceal malicious traffic, the threat actor routes it through compromised small office and home office (SOHO) network devices, including…