DarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack
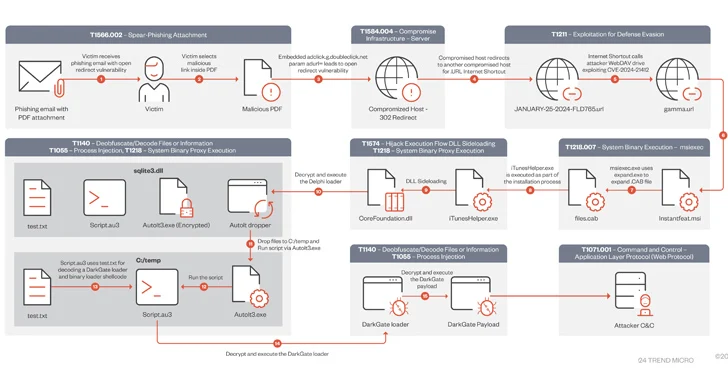
A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus software installers.
“During this campaign, users were lured using PDFs that contained Google DoubleClick Digital Marketing (DDM) open redirects that led unsuspecting victims to compromised sites hosting the Microsoft Windows SmartScreen bypass CVE-2024-21412 that led to malicious Microsoft (.MSI) installers,” Trend Micro said.
CVE-2024-21412 (CVSS score: 8.1) concerns an internet shortcut files security feature bypass vulnerability that permits an unauthenticated attacker to circumvent SmartScreen protections by tricking a victim into clicking on a specially crafted file.
It was fixed by Microsoft as part of its Patch Tuesday updates for February 2024, but not before it was weaponized by a threat actor called Water Hydra (aka DarkCasino) to deliver the DarkMe malware in attacks targeting financial institutions.
The latest findings from Trend Micro show that the vulnerability has come under broader exploitation than previously thought, with the DarkGate campaign leveraging it in conjunction with open redirects from Google Ads to proliferate the malware.
The sophisticated attack chain begins with victims clicking on a link embedded within a PDF attachment sent via a phishing email. The link deploys an open redirect from Google’s doubleclick[.]net domain to a compromised web server hosting a malicious .URL internet shortcut file that exploits CVE-2024-21412.
Specifically, the open redirects are designed to distribute fake Microsoft software installers (.MSI) masquerading as legitimate software, such as Apple iTunes, Notion, NVIDIA, which come fitted with a side-loaded DLL file that decrypted and infected users with DarkGate (version 6.1.7).
It’s worth noting that another now-fixed bypass flaw in Windows SmartScreen (CVE-2023-36025, CVSS score: 8.8) has been employed by threat actors to deliver DarkGate, Phemedrone Stealer, and Mispadu over the past few months.
The abuse of Google Ads technologies allows threat actors to increase the reach and scale of their attacks through different ad…