Feel-good story of the week: 2 ransomware gangs meet their demise
From the warm-and-fuzzy files comes this feel-good Friday post, chronicling this week’s takedown of two hated ransomware groups. One vanished on Tuesday, allegedly after being hacked by a group claiming allegiance to Ukraine. The other was taken out a day later thanks to an international police dragnet.
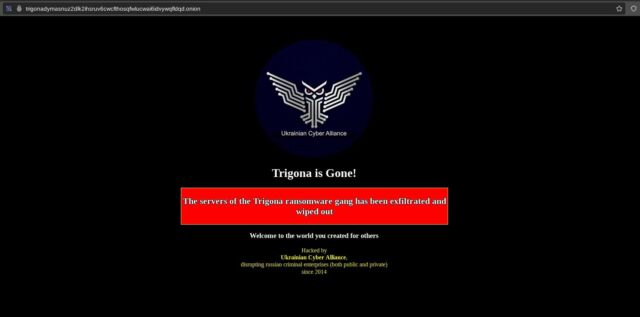
The first group, calling itself Trigona, saw the content on its dark web victim naming-and-shaming site pulled down and replaced with a banner proclaiming: “Trigona is gone! The servers of Trigona ransomware gang has been infiltrated and wiped out.” An outfit calling itself Ukrainian Cyber Alliance took credit and included the tagline: “disrupting Russian criminal enterprises (both public and private) since 2014.”
Poor operational security
A social media post from a user claiming to be a Ukrainian Cyber Alliance press secretary said his group targeted ransomware groups partly because they consider themselves out of reach of Western law enforcement.
“We just found one gang like that and did to them as they do to the rest,” the press secretary wrote. “Downloaded their servers (ten of them), deleted everything and defaced for the last time. TOR didn’t help them or even knowing they had a hole in it. Their entire infrastructure is completely blown away. Such a hunt forward.’”
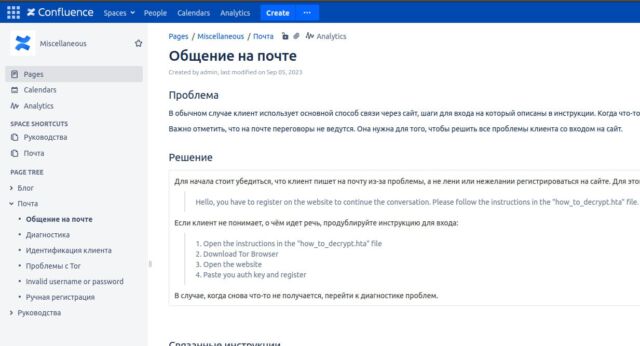
A separate social media post dumped what the press secretary said was an administrative panel key and said the group wiped out Trigona’s “landing, blog, leaks site, internal server (rocketchat, atlassian), wallets and dev servers.” The person also claimed that the Ukrainian Cyber Alliance hacked a Confluence server Trigona used.
By Friday, the Trigona site was unavailable, as evidenced by the message “Onionsite not found.”
Trigona first surfaced in 2022 with close ties to ransomware groups known as CryLock and BlackCat and looser ties to ALPHV. It primarily hacked companies in the US and India, followed by Israel, Turkey, Brazil, and Italy. It was known for compromising MYSQL servers,…


