Microsoft Issues Patches for 97 Flaws, Including Active Ransomware Exploit
It’s the second Tuesday of the month, and Microsoft has released another set of security updates to fix a total of 97 flaws impacting its software, one of which has been actively exploited in ransomware attacks in the wild.
Seven of the 97 bugs are rated Critical and 90 are rated Important in severity. Interestingly, 45 of the shortcomings are remote code execution flaws, followed by 20 elevation of privilege vulnerabilities. The updates also follow fixes for 26 vulnerabilities in its Edge browser that were released over the past month.
The security flaw that’s come under active exploitation is CVE-2023-28252 (CVSS score: 7.8), a privilege escalation bug in the Windows Common Log File System (CLFS) Driver.
“An attacker who successfully exploited this vulnerability could gain SYSTEM privileges,” Microsoft said in an advisory, crediting researchers Boris Larin, Genwei Jiang, and Quan Jin for reporting the issue.
CVE-2023-28252 is the fourth privilege escalation flaw in the CLFS component that has come under active abuse in the past year alone after CVE-2022-24521, CVE-2022-37969, and CVE-2023-23376 (CVSS scores: 7.8). At least 32 vulnerabilities have been identified in CLFS since 2018.
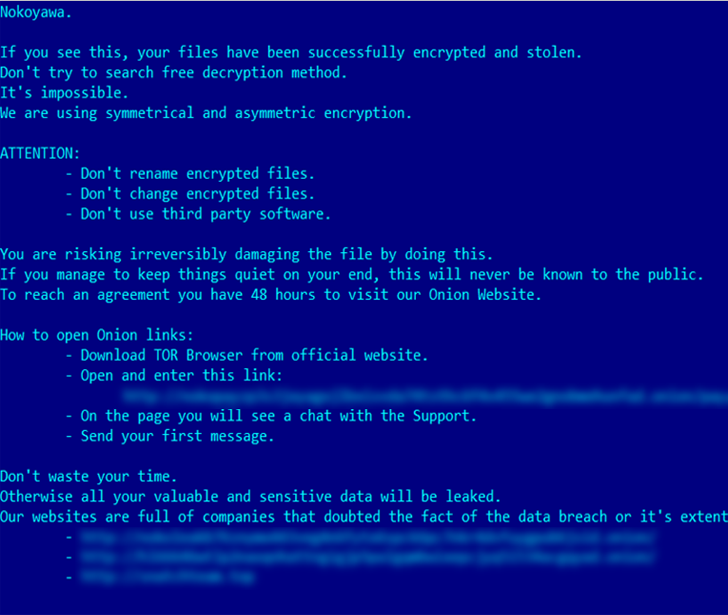
According to Russian cybersecurity firm Kaspersky, the vulnerability has been weaponized by a cybercrime group to deploy Nokoyawa ransomware against small and medium-sized businesses in the Middle East, North America, and Asia.
“CVE-2023-28252 is an out-of-bounds write (increment) vulnerability that can be exploited when the system attempts to extend the metadata block,” Larin said. “The vulnerability gets triggered by the manipulation of the base log file.”
In light of ongoing exploitation of the flaw, CISA added the Windows zero-day to its catalog of Known Exploited Vulnerabilities (KEV), ordering Federal Civilian Executive Branch (FCEB) agencies to secure their systems by May 2, 2023.
Also patched are critical remote code execution flaws impacting DHCP Server Service, Layer 2 Tunneling Protocol, Raw Image Extension, Windows Point-to-Point Tunneling Protocol, Windows Pragmatic General Multicast, and Microsoft Message Queuing (