FBI Warns of DoppelPaymer Ransomware Attack Surge
Fraud Management & Cybercrime
,
Ransomware
Cybercriminals Are Using Phone Calls to Pressure Victims

See Also: Protecting from Ransomware Attacks with DNS
The operators of DoppelPaymer, or their affiliates, have been calling victims as a way of pressuring them to pay ransoms, which can be as high as seven figures, the FBI reports in a notice made public this week.
“As of February 2020, in multiple instances, DoppelPaymer actors had followed ransomware infections with calls to the victims to extort payments through intimidation or threatening to release exfiltrated data,” the FBI alert notes. “In one case, an actor, using a spoofed U.S.-based telephone number while claiming to be located in North Korea, threatened to leak or sell data from an identified business if the business did not pay the ransom.”
First spotted in 2019 as an offshoot of the cybercrime operation called Evil Corp, DoppelPaymer – which appears to be a variant of BitPaymer – has previously hit several high-profile targets, including Mexico’s state-run oil company Pemex and Chile’s Ministry of Agriculture, according to cybersecurity analysts.
The DoppelPaymer gang demands ransoms of $25,000 to $1.2 million in bitcoin, according to a previous report by security firm CrowdStrike (see: DoppelPaymer Ransomware Gang Threatens to Dump Victims’ Data ).
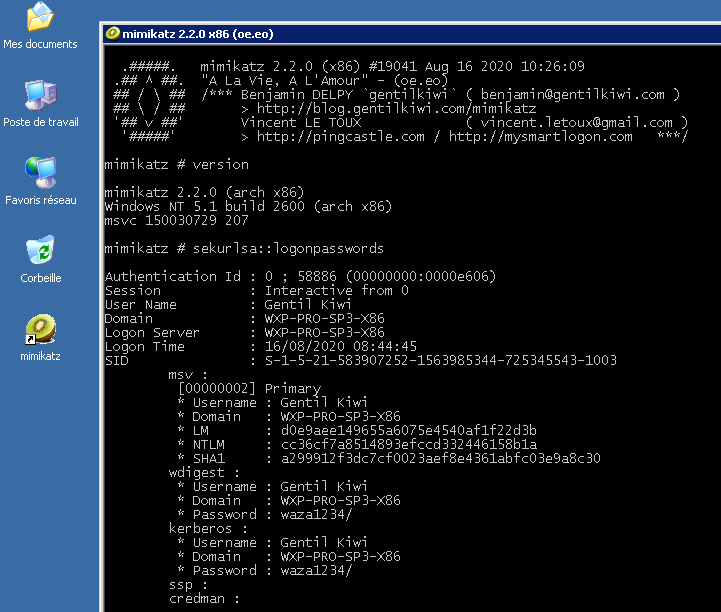
The operators of DoppelPaymer and their affiliates not only use crypto-locking malware to encrypt files within targeted networks but also exfiltrate data in an attempt to extort payments from…