California Startup to Provide Data Security for US Air Force Documents
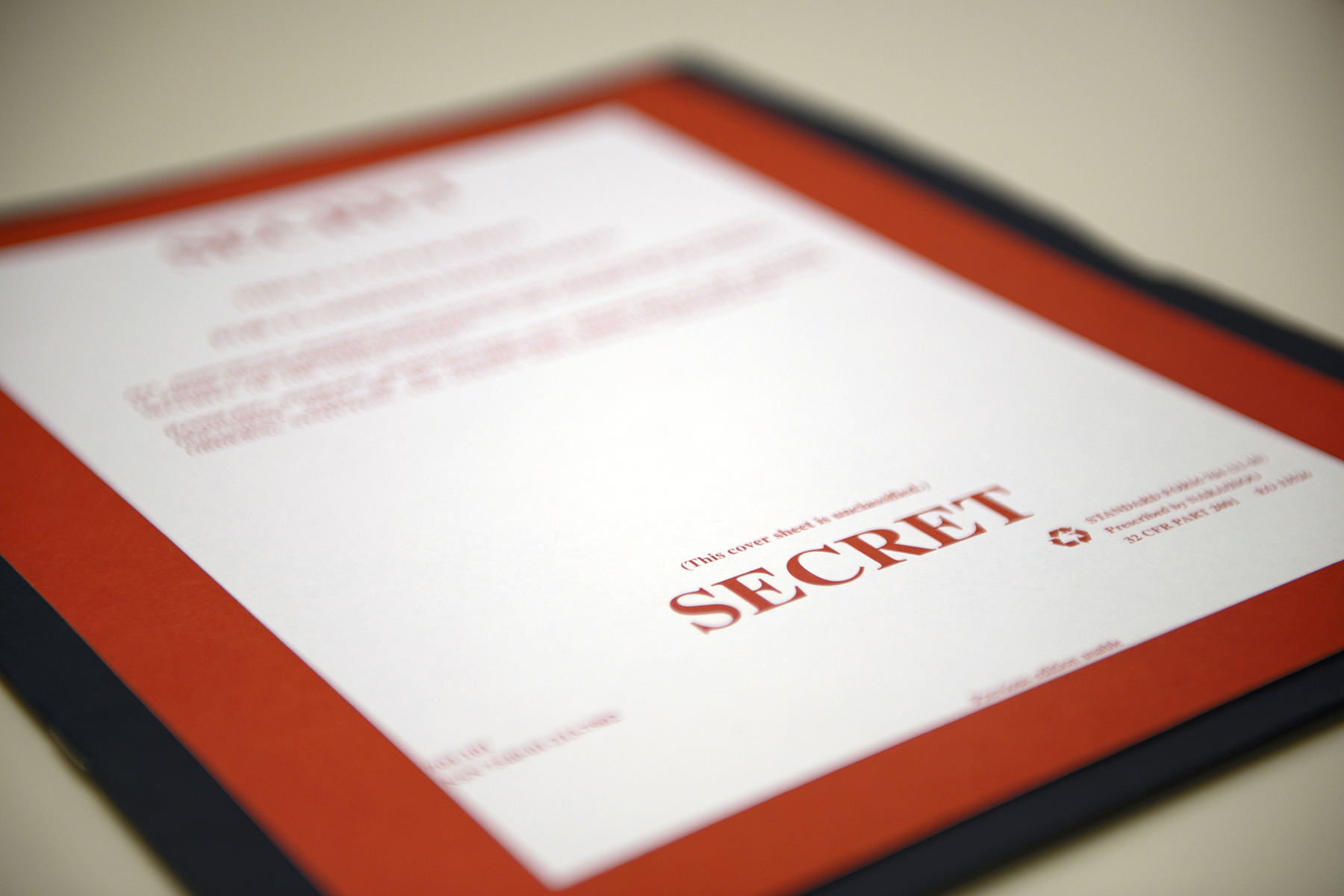
California tech firm Confidencial Inc. has signed a $1.8-million contract to provide advanced data security for the US Air Force’s collaboration tools.
The agreement will deliver a selective encryption solution to enhance productivity related to protecting sensitive national defense documents shared among the agency’s partners, contractors, and allied forces.
Assets covered under the project include various document formats, with some accessible through multi-cloud environments.
Other tasks involve file sharing, data scanning, and electronic signature services.
Work for the contract will be facilitated under the Small Business Innovation Research and Technology Transfer, a program expanding startup defense opportunities.
Led by the air force’s innovation arms AFWERX and Air Force Research Laboratory, this framework agreement promotes collaboration for a pool of industry partners to “eliminate bureaucratic overhead” and apply faster proposal timelines for continuous contract execution.
“The United States Air Force is among the most sophisticated cybersecurity organizations in the world,” Confidencial CEO Stewart Walchli stated.
“Partnering with the Air Force on this important initiative to protect unstructured data is a tremendous honor and endorsement of our technology.”
“This partnership will further strengthen our technology and capabilities, helping to ensure that our solution continues to be at the forefront of protecting unstructured data for government and commercial organizations alike.”
Latest Data Security Contracts
The US awarded CACI a $1.3-billion contract in April to deliver IT and communications end-user support for over 11,000 American warfighters based in 60 locations across Europe and Africa.
The same month, a tech consortium was established to supply wireless device detection solutions for the Pentagon’s sensitive facilities, which house vital national security data.
Simultaneously, the US government partnered with a Massachusetts-based cloud platform developer to produce a zero-trust cybersecurity prototype for US Army combat units.