Android malware posing as Google Chrome could steal your photos, contacts, and more — how to spot the fake
An updated version of the XLoader malware for Android devices doesn’t require any user interaction to launch once installed, according to researchers at McAfee (via BleepingComputer). Of course, you still need to click the malicious link in an SMS message to download and install the malware, but this XLoader variant doesn’t require users to manually launch the malware anymore.
Right now, the malware is being distributed through SMS texts on Android devices. If you’re targeted, the SMS text will include a shortened URL that, if clicked on, will direct you to a website to download an Android APK installation file for a mobile app. McAfee says that, “While the app is installed, their malicious activity starts automatically.”
The malware will run silently in the background, gaining access to all kinds of personal, private data on your Android device, including photos, messages, contacts, and potentially banking information. Luckily, the malware is pretty easy to spot and you might already be protected if Google’s Play Protect service is enabled on your Android device. Here’s what to look for, and how to see if Play Protect is active.
How to spot the new XLoader malware
XLoader—also known as MoqHao malware—is likely created by ‘Roaming Mantis,’ a financially-motivated threat actor, and McAfee identified some malicious pop-up messages in the malware’s code in English, Korean, French, Japanese, German, and Hindi, which indicates the malware’s current targets.
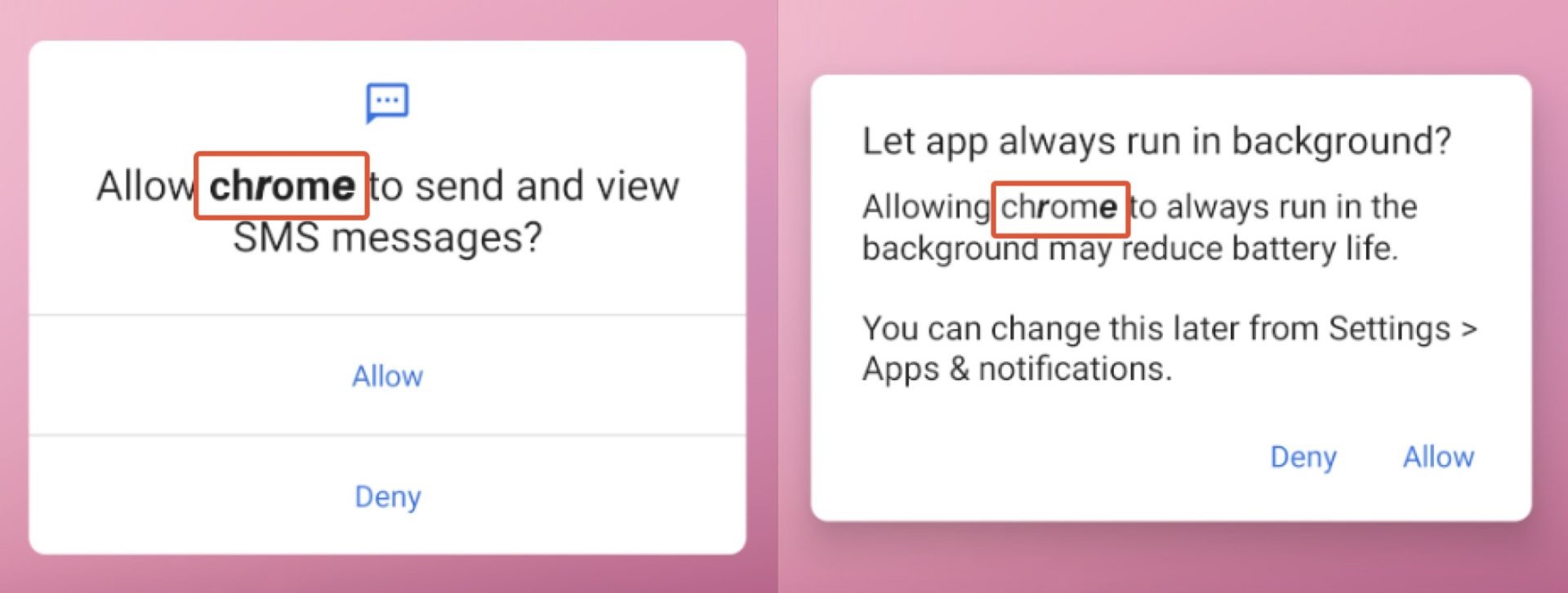
If you’re in an area that primarily speaks one of those languages, you might be at risk, but the warning signs that something’s off are pretty clear. In permission requests during the malicious app’s first launch, it’ll masquerade as Google Chrome, but you’ll notice some letters are bolded while others aren’t.
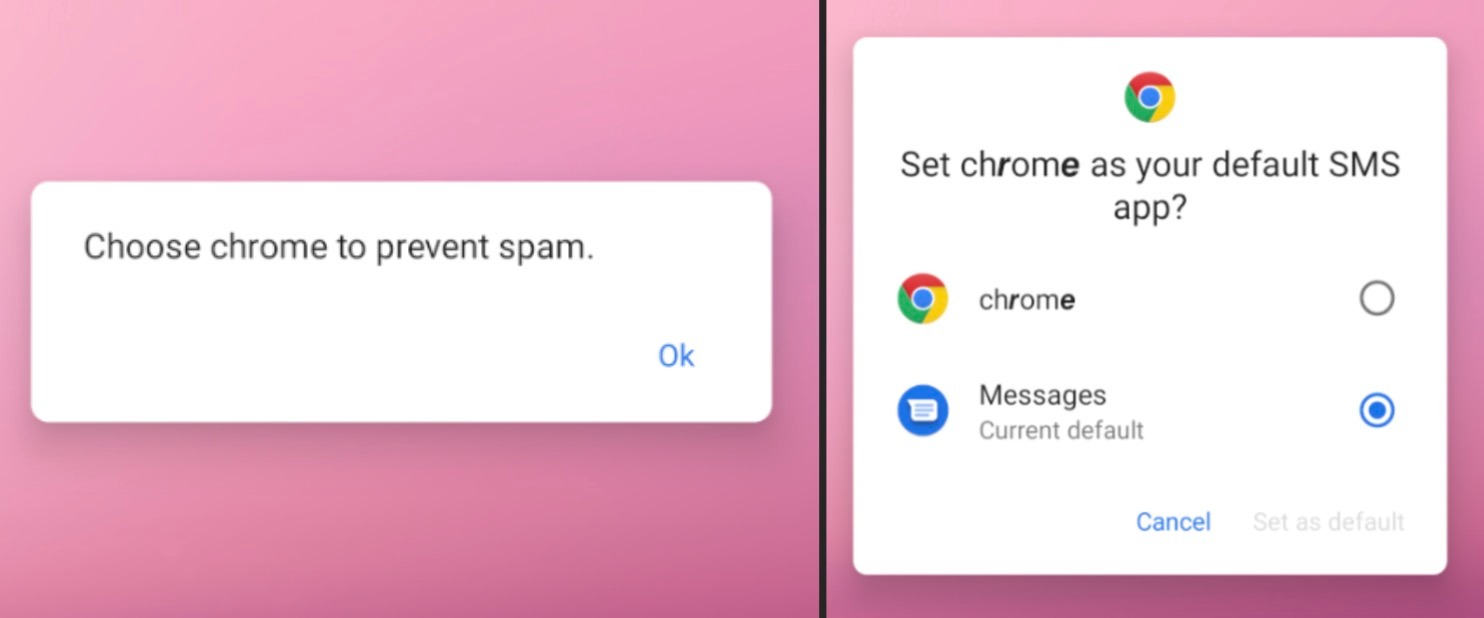
After those initial requests, the malicious app will ask you to set “chrome” as your default SMS app, citing the reason “to prevent spam” to convince you it’s the right decision. Again, you’ll spot randomly bolded letters here as a warning sign that something’s off.
You should be on the lookout for suspicious-looking phishing URLs from Pinterest profiles, as this is a primary way…