Your Android device could be affected by a crypto-mining botnet
Full coverage |
Full coverage |
Full coverage |
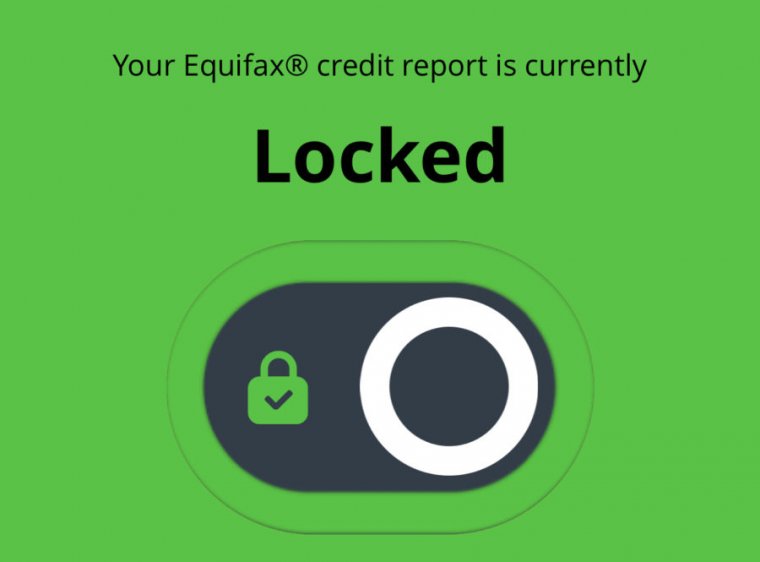
Enlarge / Now I’m protected, apparenty, after troubleshooting with Equifax.
Last week, I reported about the travails I and others experienced while trying to use a new service from Equifax called “Lock & Alert.” The service, which is front-ended by a website and a mobile application, allows individuals to place or remove a “security lock” on their credit reports with a click or a finger-swipe. After installing the app, I (and reporters from The New York Times as well) encountered some usability issues—as in, the app wasn’t working at all.
On Friday afternoon, a spokesperson for Equifax reached out to me and offered to connect me with a senior technical support person to figure out what was going on. Yesterday, we got on the phone to work out the problem. Part of the fault for my issues rested between my chair and the touchscreen of my phone, and a whole bunch more rested with the application itself and Equifax’s help line. The app is now functioning as intended. But what the app does, exactly, requires a reading of the website’s fine print.
When I set up an account from my phone, I entered my email address with a typo at the end—”.cm” instead of “.com.” Instead of telling me that I had a malformed email address (well, an address in Cameroon), the app went ahead and created the account but then gave me a mysterious error message that instructed me to call technical support. This, I was told by the Equifax tech support representative I spoke to yesterday, was a feature, not a bug: my email address had triggered a fraud warning that a human being needed to address.
Read 11 remaining paragraphs | Comments
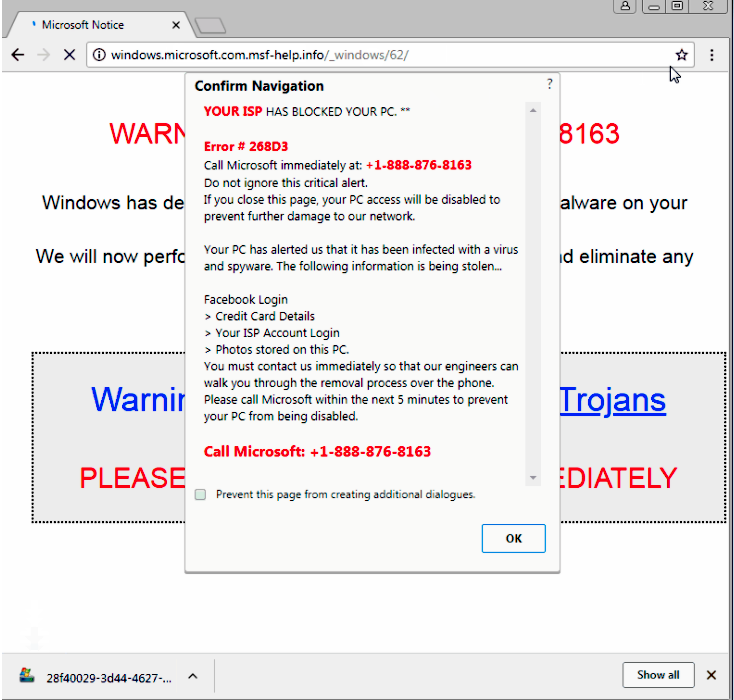
Enlarge (credit: Malwarebytes)
Con artists pushing tech-support scams have an arsenal of ways to lock up the browsers of potential marks. On Tuesday, a researcher disclosed a new weapon that freezes Google Chrome, which, by most measures, is the Internet’s most widely used browser.
The point of all the techniques is to render a browser unusable immediately after it displays a fake error message reporting some sort of security breach. Given the appearance of a serious crash that can’t be fixed simply by exiting the site, end users are more likely to be worked into a panic and call the phone number included in the warning. Once called, the scammers—posing as representatives from Microsoft or another legitimate company—stand a better chance of tricking the caller into providing a credit card number in return for tech support to fix the non-existent security problem. The scams are often transmitted through malicious advertisements or legitimate sites that have been hacked.
A new technique reported by security provider Malwarebytes works against Chrome by abusing the programming interface known as the window.navigator.msSaveOrOpenBlob. By combining the API with other functions, the scammers force the browser to save a file to disk, over and over, at intervals so fast it’s impossible to see what’s happening. Within five to 10 seconds, the browser becomes completely unresponsive. Users are left viewing a page that looks like the left side of this image:
Read 8 remaining paragraphs | Comments