Computer hacking may never fully go away even with the best new technology — and we may not want it to
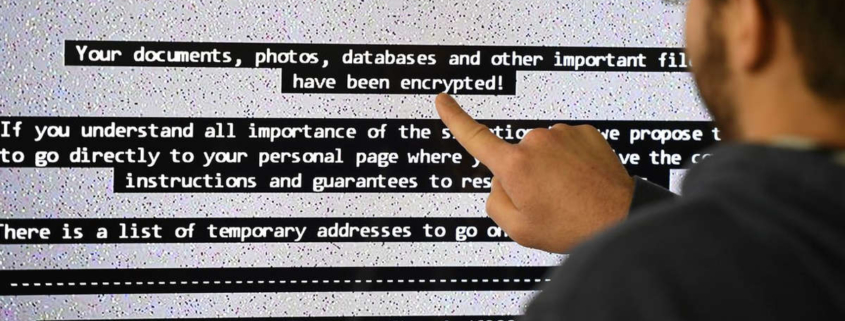
This wasn’t the first, nor it will be the last, such attack. However, certain details made cybersecurity experts worried: First, hackers used a zero-day exploit, i.e. a yet unknown flaw in the code, to execute their attack. Second, they targeted a company that isn’t as valuable a target as a bank, for example, but has a strategic significance due to its connection with the companies it serves.
According to experts, independent hackers are upping their game, employing advanced tools and strategies, acting like elite government-backed hackers, rather than mere criminals.
While I don’t necessarily disagree with this assessment, I can’t help but wonder if these experts have underestimated the global hacker community? Also, it is as if they’re not aware of the state and rapid growth of global data infrastructure.
Globalization and unification
We live in the era where digital globalization and unification have reached the highest levels in history. In addition to some benefits, this also brought multiple risks to the table.
One is centralization. Instead of having a decentralized structure that is fragmented across multiple nodes, the data is often stored in a unified system, which means there is a singular point of failure. When that system gets breached eventually, the attacker can gain access to more information and power than he would’ve had if he had accessed a walled-off segment of the same system.
This is especially the case with cloud-based services. The monopoly power of tech giants and service providers growing across the developed world is another pain point as it ensures that a handful of companies provides services to the vast majority of enterprises that share a unified infrastructure and software backbone.
While it may not be obvious to those less tech-savvy, it’s quite easy even for a newbie hacker to discern what operating system (OS), content management system (CMS), marketing technology (martech) platform or other point of entry his victims use, and what kind of vulnerabilities — if any — exist for the version the victim is currently using.
All that’s left is to execute the attack and cover his tracks.
Social engineering
Finally, one must…