DarkSide ransomware’s Iranian hosting raises U.S. sanction concerns

Ransomware negotiation firm Coveware has placed the DarkSide operation on an internal restricted list after the threat actors announced plans to host infrastructure in Iran.
When the DarkSide ransomware operation encrypts a network, their affiliates steal unencrypted files, which they threaten to release if a ransom is not paid.
This double-extortion strategy is always under attack by law enforcement and security firms who try to disrupt or take down ransomware data leak sites where stolen files are published.
DarkSide plans to host infrastructure in Iran
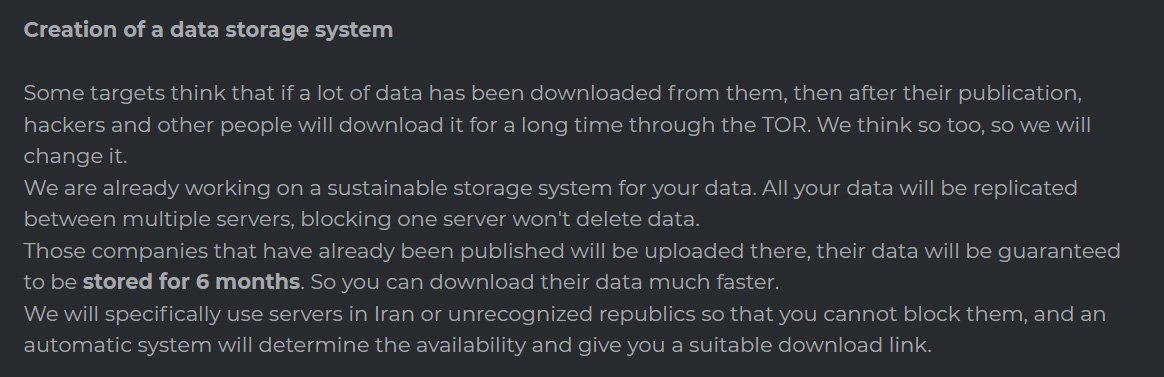
To prevent their data leak service from being taken down, the DarkSide gang announced this week that they are building a distributed and sustainable storage system in Iran and other “unrecognized republics.” With this system, if one server is taken down, the data will still remain and be available on the other servers.
In October, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) issued an advisory that warned ransomware negotiators and U.S. businesses that paying ransom could lead to sanction violations and fines.
As examples of sanctioned hacking groups that are known to deal with ransomware, the advisory mentioned:
- Sanctioned the developer of Cryptolocker ransomware, Evgeniy Mikhailovich Bogachev, in December 2016 (Cryptolocker was used to infect more than 234,000 computers starting in 2013, approximately half of which were in the US)
- Sanctioned two Iranians for providing material support to SamSam ransomware in November 2018 (SamSam was used to target mostly U.S. government institutions and companies starting in late 2015 and lasting approximately 34 months)
- Lazarus Group and two sub-groups, Bluenoroff and Andariel, were sanctioned in September 2019 (these groups were linked to WannaCry 2.0 ransomware that infected approximately 300,000 computers in at least 150 countries in May 2017)
- Evil Corp and its leader, Maksim Yakubets, were sanctioned in December 2019 (the Russia-based cybercrime organization used Dridex malware harvest login credentials from hundreds of banks and financial institutions in over 40 countries, causing more than $100…

