DNSpooq bugs let attackers hijack DNS on millions of devices

Israel-based security consultancy firm JSOF disclosed today seven Dnsmasq vulnerabilities, collectively known as DNSpooq, that can be exploited to launch DNS cache poisoning and remote code execution against millions of affected devices.
Dnsmasq is a popular and open-source Domain Name System (DNS) forwarding software that adds DNS caching and Dynamic Host Configuration Protocol (DHCP) server capabilities to networking equipment it runs on.
The full number or the name of all companies that use Dnsmasq versions vulnerable to DNSpooq attacks on their devices is not yet known.
However, JSOF highlighted a list of 40 vendors in their report, including Android/Google, Comcast, Cisco, Redhat, Netgear, Qualcomm, Linksys, Netgear, IBM, D-Link, Dell, Huawei, and Ubiquiti.
Behind the DNSpooq vulnerabilities
Three of the DNSpooq vulnerabilities (tracked as CVE-2020-25686, CVE-2020-25684, CVE-2020-25685) allow for both DNS cache poisoning attacks (also known as DNS spoofing).
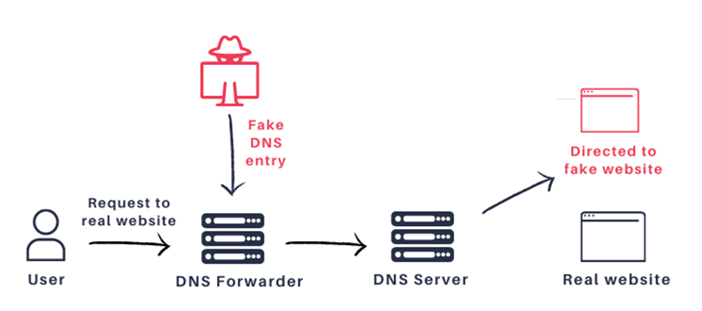
DNS Cache Poisoning is an attack method that allows threat actors to replace legitimate DNS records on a device with ones of their choosing.
Using this attack, threat actors can redirect users to malicious servers under their control, while to the visitors it appears as if they are visiting the legitimate site.
This allows the attackers to perform phishing attacks, credential theft, or to distribute malware from what is perceived as a trusted company.
The first DNS spoofing attack was disclosed by security researcher Dan Kaminsky in 2008 when he showed that DNS software can be exploited to steal data and impersonate any website name.
“Traffic that might be subverted includes regular Internet browsing as well as other types of traffic, such as emails, SSH, remote desktop, RDP video and voice calls, software updates, and so on,” JSOF’s report explains.
Hypothetical attack scenarios also include JavaScript-fueled Distributed Denial of Service (DDoS), reverse DDOS, and wormable attacks in the case of mobile devices that switch networks regularly.
The rest of them are buffer overflow vulnerabilities tracked as CVE-2020-25687, CVE-2020-25683, CVE-2020-25682, and CVE-2020-25681 that…


