Hackers Score Nearly $1M at Device-Focused Pwn2Own Contest
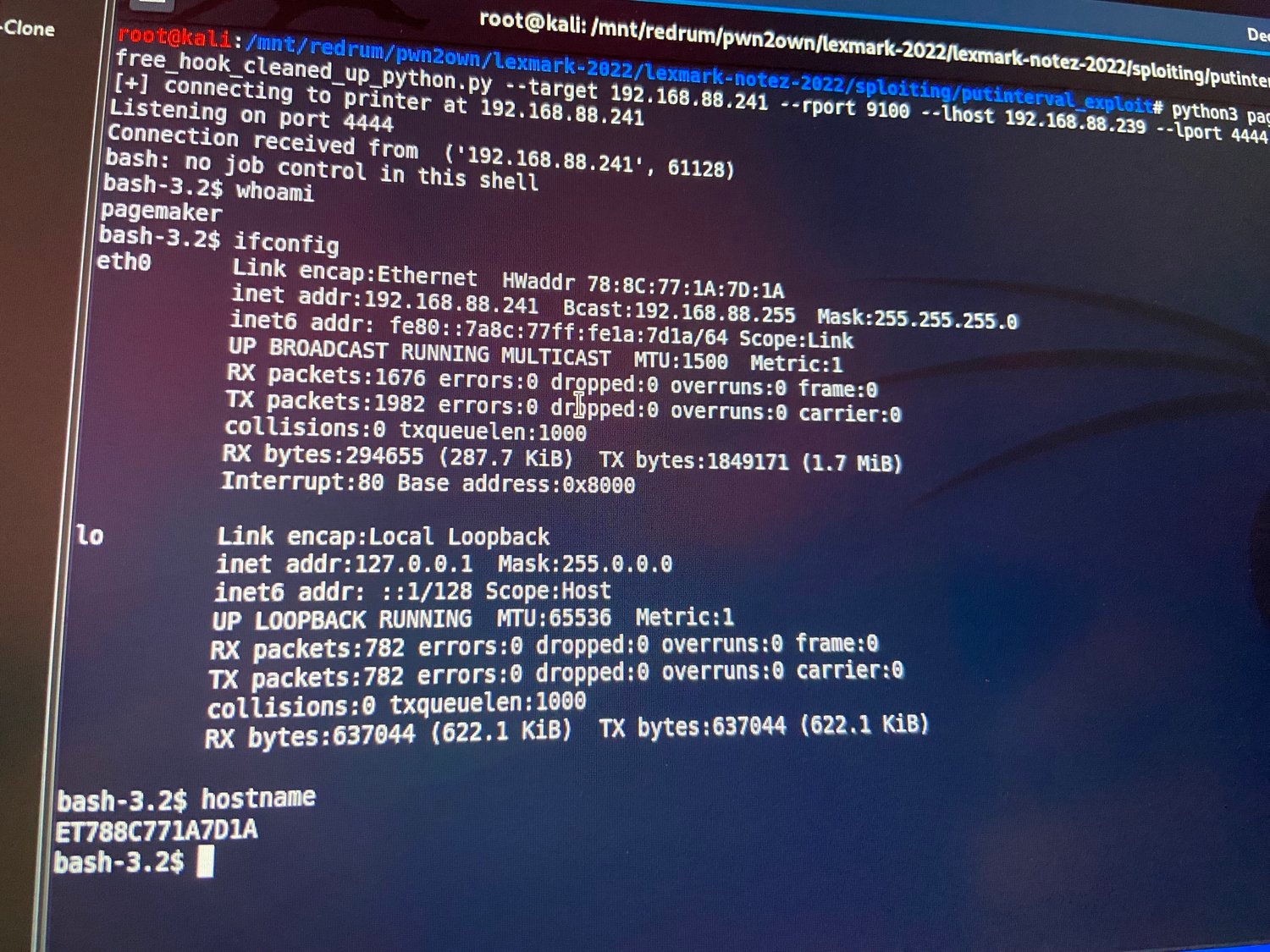
Security researchers and hackers demonstrated 63 zero-day vulnerabilities in popular devices at the latest Pwn2Own, exploiting printers from Canon, HP, and Lexmark, and routers and network-attached storage device from Synology and Netgear.
According to Trend Micro’s Zero Day Initiative (ZDI), which organized the competition last week, the collection of vulnerabilities earned $989,750 for the offensive cybersecurity specialists competing in the contest. While some attacks chained together a series of exploits to take control of the remote devices, including one that used five vulnerabilities, others found a single security weakness to target, such as the Pentest Limited team, which found a reliable single-click exploit in the Samsung Galaxy S22 mobile phone that required less than a minute to attack.
The Samsung exploit highlighted that significant vulnerabilities are out there to find, says Dustin Child, head of threat awareness at Trend Micro’s Zero Day Initiative.
“Just click a link on an affected device and you get owned,” he says. “It’s a very reliable bug, too. Very impressive research and quite the effective demonstration of why clicking unknown links can be dangerous.”
Focusing on IoT and Mobile
Pwn2Own started in 2007 as an annual contest connected with the annual CanSecWest conference, but has since branched out into two contests: one focused on computer operating systems and applications, and the other — which includes the latest contest — focused on devices and the Internet of Things.
Over the four days of the contest, offensive cybersecurity specialists discovered a significant number of vulnerabilities in printers and routers from major brands, but also targeted Bluetooth speakers and network-attached storage, ZDI stated in a summary of the contest results.
Because many of the devices are commonly used by small and medium-sized businesses (SMBs), companies should take the results of the competition as a warning, Child says.
“If anything, SMBs should understand that, while they may feel they aren’t large enough to be a target, their devices can and will be targeted by threat actors,” he says. “At [this] time, the attackers are just looking to add nodes to their botnet,…