Malware Attack Can Lead To Data Loss | by PITS Global Data Recovery Services | Aug, 2023
With the rise of technology and interconnectivity, the threat of data loss has also grown significantly. One of the most dangerous culprits responsible for data loss is malware. In this blog, we will explain the world of malware, its potential consequences, and the measures you can take to safeguard your data.
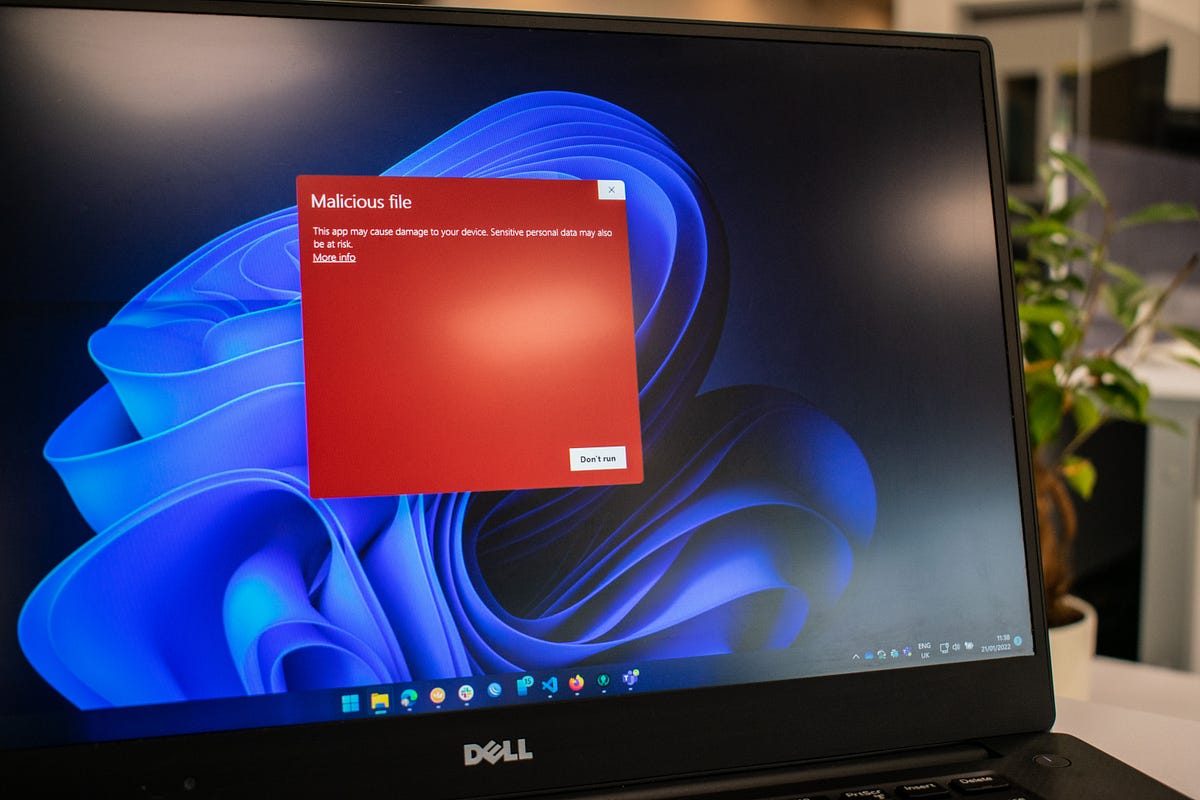
Malware, short for “malicious software,” refers to a broad category of software programs designed with malicious intent. Malware is created to gain unauthorized access to systems, steal sensitive information, disrupt computer operations, or cause harm in various ways. Malware can take many forms, including viruses, worms, Trojans, ransomware, spyware, and adware.
- Data Theft: One of the primary objectives of malware attacks is to steal valuable data. Cybercriminals may target personal information like login credentials, credit card details, and social security numbers. In the case of businesses, sensitive customer data, intellectual property, and financial records are often the primary targets. Once in the hands of malicious actors, this data can be sold on the dark web, used for identity theft, or leveraged for extortion.
- Ransomware: Ransomware is a type of malware that encrypts a victim’s data, making it inaccessible until a ransom is paid. Falling prey to a ransomware attack can lead to significant data loss, as organizations might lose access to their critical files and databases. Even if the ransom is paid, there is no guarantee that the attackers will decrypt the data, leaving victims in a devastating situation.
- Data Destruction: Some malware is designed explicitly to cause data destruction. These destructive malware types can wipe out entire data systems, rendering them unusable and causing severe data loss. Such attacks can lead to costly downtime, loss of productivity, and reputational damage.
- Disruption of Backups: Backups are essential for data recovery in the event of a data loss event. However, advanced malware can infect backup systems, compromising the ability to restore data effectively. If backups are not securely isolated from the network, they may also be subject to the same vulnerabilities as primary data storage.