Phishing, Malware and Hacker Groups Taking Sides
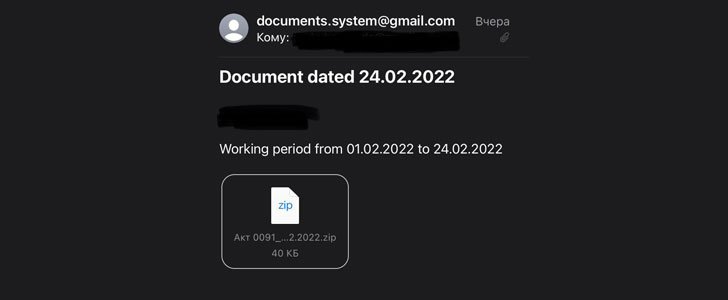
Ukraine’s Computer Emergency Response Team (CERT-UA) has warned of Belarusian state-sponsored hackers targeting its military personnel and related individuals as part of a phishing campaign mounted amidst Russia’s military invasion of the country.
“Mass phishing emails have recently been observed targeting private ‘i.ua’ and ‘meta.ua’ accounts of Ukrainian military personnel and related individuals,” the CERT-UA said. “After the account is compromised, the attackers, by the IMAP protocol, get access to all the messages.”
Subsequently, the attacks leverage the contact information stored in the victim’s address book to propagate the phishing messages to other targets.
The Ukrainian government attributed the activities to a threat actor tracked as UNC1151, a Minsk-based group whose “members are officers of the Ministry of Defence of the Republic of Belarus.” In a follow-up update, the agency said the nation-state group also targets its own citizens, while simultaneously setting its sights on Russian entities –
- Association of Belarusians of the World (International Social Union)
- Belarusian Music Festival
- Samara Oblasna Public Organization “Russian-Belarusian Fraternity 2000”
- Dzêâslov, a Belarusian literary magazine
- Soviet Belarus (Sovetskaya Belorussiya), a daily newspaper in Belarus
- Employees of the National Academy of the Republic of Kazakhstan, and
- Voice of the Motherland, a local newspaper in Belarus
UNC1151 is the Mandiant-assigned moniker to an uncategorized threat cluster, which operates with objectives that are aligned with Belarusian government interests. The hacking group is believed to have been active since at least 2016.
“UNC1151 has targeted a wide variety of governmental and private sector entities, with a focus in Ukraine, Lithuania, Latvia, Poland, and Germany,” Mandiant researchers said in a November 2021 report. “The targeting also includes Belarusian dissidents, media entities, and journalists.”
The state-backed cyber espionage group has also been linked to the Ghostwriter disinformation campaign that promulgated anti-NATO and corruption-themed narratives aimed at Lithuania, Latvia, and Poland with the likely goal of undermining the governments and creating…